CCIE
now browsing by category
Latest Cisco CCIE 400-251 dumps – 400-251 Practice Test Questions and Answers
We share the latest exam dumps throughout the year to help you improve your skills and experience! The latest Cisco CCIE 400-251 exam dumps, online exam Practice test to test your strength, Cisco 400-251 “400-251 CCIE Security written exam” in https://www.leads4pass.com/400-251.html Update
the exam content throughout the year to ensure that all exam content is authentic and valid. 400-251 PDF Online download for easy learning.
[PDF] Free Cisco CCIE 400-251 pdf dumps download from Google Drive: https://drive.google.com/open?id=1izuLzJAFClLatQZtmzmy_cnCuTi-mfLy
[PDF] Free Full Cisco pdf dumps download from Google Drive: https://drive.google.com/open?id=1CMo2G21nPLf7ZmI-3_hBpr4GDKRQWrGx
400-251 CCIE Security – Cisco: https://www.cisco.com/c/en/us/training-events/training-certifications/exams/current-list/400-251-ccie-security.html
Free test Cisco CCIE 400-251 Exam questions and Answers
QUESTION 1
Which statement about the wireless security technologies is true?\\’
A. WPA2-PSK mode provides better security by having the same passphrase across the network
B. WPA2 provides message integrity using AES
C. WPA2-PSK mode does not allow a passphrase? to be stored lo~cally on the device
D. WPA2 is more secure than WPA because it uses TKIP for encryption
E. WEP is more secure than WPA2 because it uses AES for encryption
F. WPA2-ENT mode does not require RADIUS for authentication
Correct Answer: B
QUESTION 2
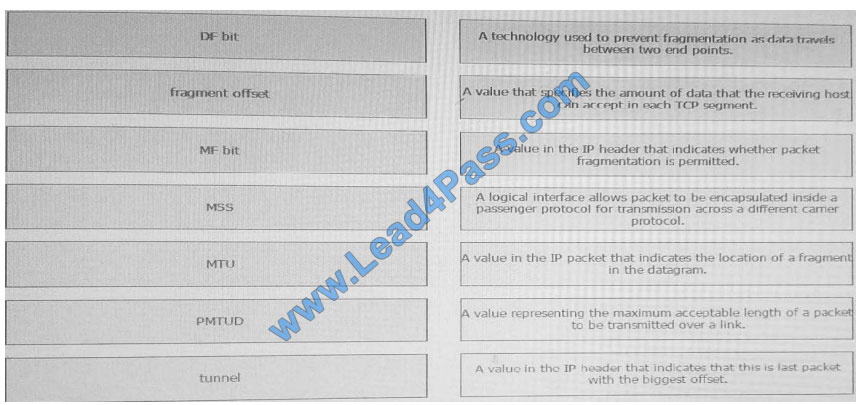
Drag each IP transmission and fragmentation term on the left to the matching statement on the right?
Select and Place: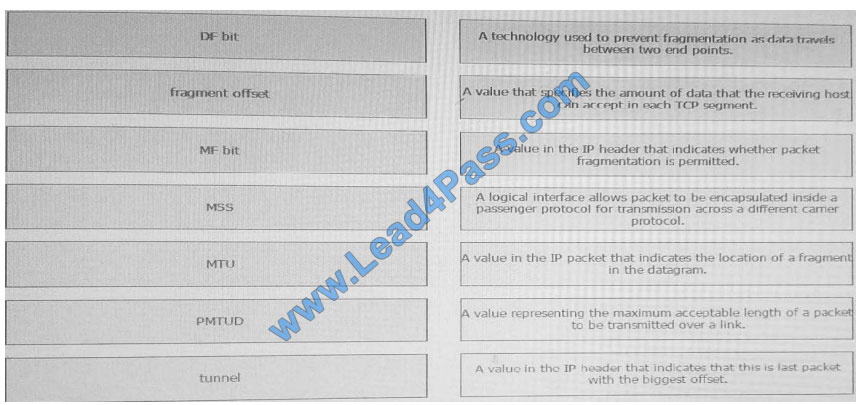
Correct Answer:
QUESTION 3
A hosted service provider is planning to use firewall contexts in its multitenant environment and will manage these
firewalls on behalf of its customers and allow them access to it for monitoring. For management purposes, the lead
architect of the service provider has decided to connect this management interface to a single shared management
zone VLAN (901) and allocate each context a unique IP form the assigned range of this VLAN. Which three statements
about this design are true? (Choose three)
A. Though this design is valid, a physical interface cannot be allocated to multiple contexts due to ASA traffic classifier
restrictions; this is only possible with subinterfaces.
B. This design concept is valid and requires some modifications. However, it would be more secure to only allow
customer management access from the data VLANs in their hosted environment to ensure adequate Layer 2/ Layer 3
separation between tenants
C. The ASA multi-context traffic classifier works differently for shared interfaces that exist on the same VLAN and have
the same MAC address when NAT is in use, other rules are applied when NAT is not in use.
D. The ASA classifier works only for data interfaces and not for management interfaces. The No Management-only
the command must be applied for this concept to work.
E. This design concept is not valid because it is not possible to allocate a physical interface to all contexts due to ASA
traffic classifier restrictions, this is only possible with subinterfaces.
F. Subinterfaces of the interface can be allocated only to contexts and not the actual management physical interface
G. The design for the management zone does not work unless unique MAC addresses are assigned
Correct Answer: CDG
QUESTION 4
Which three statements about the keying methods used by MACSec are true? (Choose three)
A. SAP is not supported on switch SVls.
B. SAP is supported on SPAN destination ports.
C. MKA is implemented as an EAPoL packet exchange.
D. Key management for host-to-switch and switch-to-switch MACSec sessions is provided by MKA.
E. SAP is enabled by default for Cisco TrustSec in manual configuration mode.
F. A valid mode for SAP is NULL.
Correct Answer: ACF
QUESTION 5
Which three EAP protocols are supported in WPA and WPA2? (Choose three)
A. EAP-PSK
B. EAP-EKE
C. EAP-FAST
D. EAP-AKA
E. EAP-SIM
F. EAP-EEE
Correct Answer: CDE
QUESTION 6
Which statement about Dynamic ARP inspection is true?
A. It requires that DHCP snooping be disabled to build a valid binding database
B. It validates ARP requests and responses on untrusted ports using the MAC address table
C. It drops invalid ARP responses and requests on the switch untrusted ports
D. It validates ARP requests and responses on trusted ports using IP-to-MAC address binding
E. It is supported only in DHCP environments to detect invalid ARP requests and responses
F. It forwards invalid ARP responses and requests on switch untrusted ports
Correct Answer: C
QUESTION 7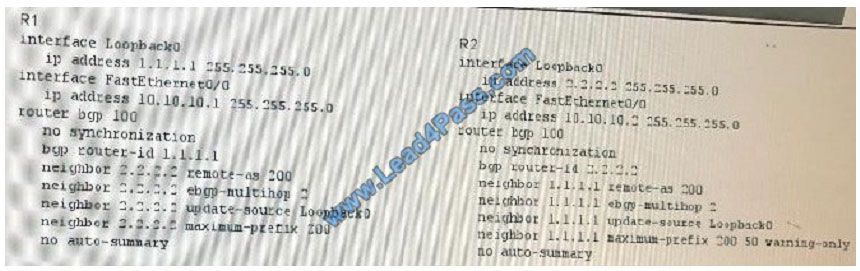
Refer to the exhibit. Which two effects of this configuration are true? (Choose two)
A. The BGP neighbor session between R1 and R2 re-establishes after 100 minutes.
B. A warning message is displayed on R2 after it receives 50 prefixes.
C. A warning message is displayed on R2 after it receives 100 prefixes from neighbor 1.1.1.1.
D. The BGP neighbor session between R1 and R2 re-establishes after 50 minutes.
E. The BGP neighbor session tears down after R1 receive 100 prefixes from neighbor 1.1.1.1.
F. The BGP neighbor session tears down after R1 receive 200 prefixes from neighbor 2.2.2.2.
Correct Answer: CF
QUESTION 8
Which statement is true about VRF-lite implementation in a service provider network?
A. It requires multiple links between CE and PE for each VPN connection to enable privacy
B. It uses the source address to differentiate routes for different VPNs on the CE device
C. It can only support one VRF instance per CE device
D. It can have multiple VRF instances associated with a single interface on a CE device
E. It supports multiple VPNs at a CE device but their address spaces should not overlap
F. It enables the sharing of one CE device among multiple customers
Correct Answer: F
QUESTION 9
A user attempts to browse the internet through a CWS-integrated router, and the HTTP 403 Forbidden error message is
returned. Which reason for the problem is the most likely?
A. The connection timed out
B. The CWS license has expired
C. The user attempted to access a web site that is blocked by CWS policy
D. User authentication failed
E. The user is not logged in to CWS
F. The CWS connector is down
Correct Answer: B
QUESTION 10
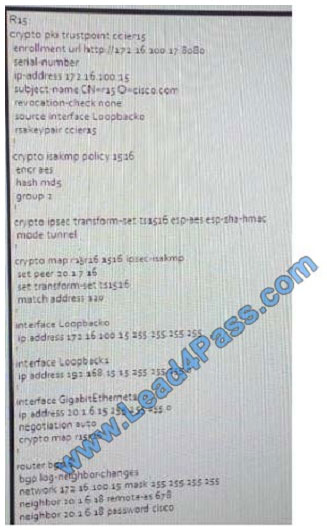
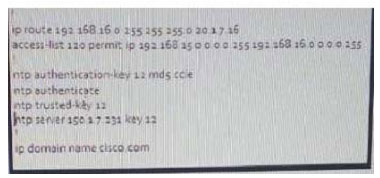
Refer to the exhibit. RlS is building a Site-To-Site IPSec certificate based VPN tunnel with a peer at 20.1.7.16. TheCA is
running at port 80 on address 172.16.100.18. R15 has a BGP peer at 20.1.6.18 doing an authenticated session to
establish reachability with the VPN remote site. The VPN tunnel secures traffic between 192.168.15.0/24 and
192.168.16.0/24 network. It has been reported that a VPN tunnel is not coming up with the remote site. Which two
possible issues are true? (Choose two)
A. Incorrect trustpoint configuration
B. Incorrect BGP peer configuration
C. Incorrect static route
D. Incorrect transform set configuration
E. Incorrect crypto map configuration
F. Incorrect ISAKMP policy configuration
G. Incorrect ACL defined for the traffic encryption
Correct Answer: AF
QUESTION 11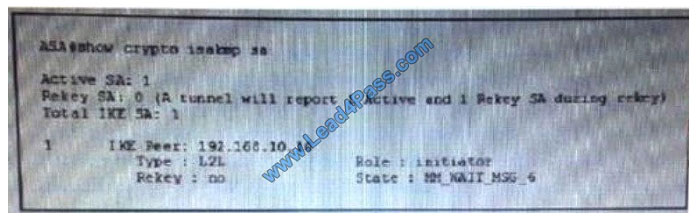
Refer to the exhibit, you issued the show crypt isakmp SA command to troubleshoot connection failure on IPsec VPN.
What possible issue does the given output indicate?
A. The peer is failing to respond
B. The crypto ACLs are mismatched
C. The pre-shared keys are mismatched
D. The transform sets are mismatched
Correct Answer: A
QUESTION 12
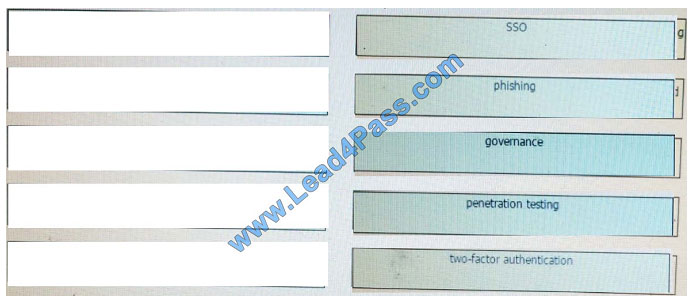
Drag and drop the desktop-security terms from the left onto their right definitions on the right?
Select and Place: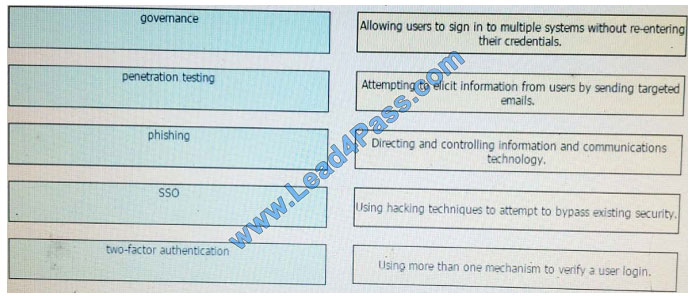
Correct Answer:
QUESTION 13
Which statement is correct regarding the SenderBase functionality?
A. ESA sees a high negative score from SenderBase as very unlikely that the sender is sending spam.
B. SenderBase uses the DNS-based blacklist as one of the sources of information to define the reputation score of the sender\\’s IP
address.
C. WSA uses SenderBase information to configure URL filtering policies.
D. ESA uses destination address reputation information from SenderBase to configure mail policies.
E. SenderBase uses spam complaints as one of the sources of information to define the reputation score of the receiver IP
address.
F. ESA sees a high positive score from SenderBase as very likely that the sender is sending spam.
Correct Answer: B
We share 13 of the latest Cisco CCIE 400-251 exam dumps and 400-251 pdf online download for free. Now you know what you’re capable of! If you’re just interested in this, please keep an eye on “examvcesuite.com” blog updates! If you want to get the Cisco CCIE 400-251 Exam Certificate: https://www.leads4pass.com/400-251.html (Total questions: 587 Q&A).
Related 400-251 Popular Exam resources
Lead4pass Promo Code 12% Off
Why Choose Lead4pass?
Lead4Pass helps you pass the exam easily! We compare data from all websites in the network, other sites are expensive,
and the data is not up to date, Lead4pass updates data throughout the year. The pass rate of the exam is above 98.9%.