L A T E S T P O S T S
-
CompTIA CAS-004 CASP+ Exam Solutions | Latest CAS-004 Dumps
-
[Updated May 2023] Practice the latest CCNP Security 350-701 exam questions online
-
Practice for the 350-901 DEVCOR exam with newly updated 350-901 dumps
-
best plans for CCNA 200-301 certification exam in 2023
-
Lead4Pass CCDP 300-910 dumps are the best material for the 300-910 DEVOPS exam
-
Get Live update CCNP Enterprise 350-401 dumps with PDF and VCE
-
CCNP Collaboration exam dumps sharing from Lead4Pass
-
Latest updated CCNP Security 300-725 dumps from Lead4Pass
-
Latest Updated CCNP Security 300-710 Dumps Helps Candidates Pass 300-710 SNCF Exam
-
VMware 5v0-11.21 dumps: serves all 5v0-11.21 VMware Cloud on AWS Master Specialist exam candidates
CompTIA CAS-004 CASP+ Exam Solutions | Latest CAS-004 Dumps
Lead4Pass CAS-004 Dumps contains 406 latest exam questions and answers, covering more than 90% of CompTIA CAS-004 “CompTIA Advanced Security Practitioner (CASP+)” actual exam questions! For your best Exam Solutions.
Lead4Pass CAS-004 exam questions and answers are updated throughout the year! Guaranteed to be available anytime! Download CAS-004 Dumps: https://www.leads4pass.com/cas-004.html
One-time use 365 days free update! You can also choose the learning method that suits you according to your learning habits: PDF and VCE learning formats are provided to help you learn easily and pass CompTIA CAS-004 CASP+ Exam successfully.
Here you can always get more: Lead4Pass CAS-004 dumps page provides download free Demo for you to experience, you can also participate in the following online practice tests
Latest CompTIA CAS-004 dumps Exam Questions
| From | Number of exam questions | Associated certification | Last update | Online Download |
| Lead4Pass | 13 | CompTIA Advanced Security Practitioner | CAS-004 dumps | CAS-004 PDF |
NEW QUESTION 1:
A company is migrating from company-owned phones to a BYOD strategy for mobile devices. The pilot program will start with the executive management team and be rolled out to the rest of the staff in phases. The company\’s Chief Financial Officer loses a phone multiple times a year.
Which of the following will MOST likely secure the data on the lost device?
A. Require a VPN to be active to access company data.
B. Set up different profiles based on the person\’s risk.
C. Remotely wipe the device.
D. Require MFA to access company applications.
Correct Answer: C
NEW QUESTION 2:
A review of the past year\’s attack patterns shows that attackers stopped reconnaissance after finding a susceptible system to compromise.
The company would like to find a way to use this information to protect the environment while
still gaining valuable attack information.
Which of the following would be BEST for the company to implement?
A. A WAF
B. An IDS
C. A SIEM
D. A honeypot
Correct Answer: D
Reference: https://www.kaspersky.com/resource-center/threats/what-is-a-honeypot
NEW QUESTION 3:
Leveraging cryptographic solutions to protect data that is in use ensures the data is encrypted:
A. when it is passed across a local network.
B. in memory during processing
C. when it is written to a system\’s solid-state drive.
D. by an enterprise hardware security module.
Correct Answer: B
NEW QUESTION 4:
A security analyst receives an alert from the SIEM regarding unusual activity on an authorized public SSH jump server.
To further investigate, the analyst pulls the event logs directly from /var/log/auth.log: graphic.ssh_auth_log.
Which of the following actions would BEST address the potential risks of the activity in the logs?
A. Alerting the misconfigured service account password
B. Modifying the AllowUsers configuration directive
C. Restricting external port 22 access
D. Implementing host-key preferences
Correct Answer: B
NEW QUESTION 5:
An organization wants to perform a scan of all its systems against best-practice security configurations.
Which of the following SCAP standards, when combined, will enable the organization to view each of the configuration checks in a machine-readable checklist format for fill automation? (Choose two.)
A. ARF
B. XCCDF
C. CPE
D. CVE
E. CVSS
F. OVAL
Correct Answer: BF
Reference: https://www.govinfo.gov/content/pkg/GOVPUB-C13-9ecd8eae582935c93d7f410e955dabb6/pdf/GOVPUB-C139ecd8eae582935c93d7f410e955dabb6.pdf (p.12)
NEW QUESTION 6:
A software company is developing an application in which data must be encrypted with a cipher that requires the following:
1.
Initialization vector
2.
Low latency
3.
Suitable for streaming
Which of the following ciphers should the company use?
A. Cipher feedback
B. Cipher block chaining message authentication code
C. Cipher block chaining
D. Electronic codebook
Correct Answer: C
Reference: https://www.sciencedirect.com/topics/computer-science/symmetric-cipher
NEW QUESTION 7:
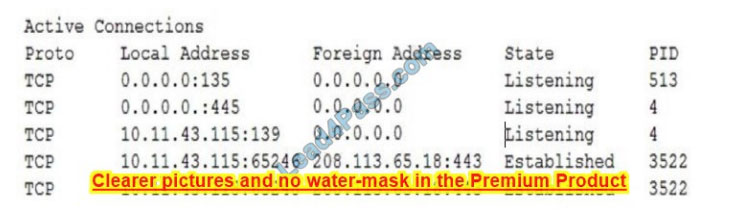
Ann. a user, brings her laptop to an analyst after noticing it has been operating very slowly. The security analyst examines the laptop and obtains the following output: Which of the following will the analyst most likely use NEXT?
A. Process explorer
B. Vulnerability scanner
C. Antivirus
D. Network enumerator
Correct Answer: B
NEW QUESTION 8:
A company\’s product site recently had failed API calls, resulting in customers being unable to check out and purchase products. This type of failure could lead to the loss of customers and damage to the company\’s reputation in the market.
Which of the following should the company implement to address the risk of system unavailability?
A. User and entity behavior analytics
B. Redundant reporting systems
C. A self-healing system
D. Application controls
Correct Answer: D
NEW QUESTION 9:
A Chief Information Officer is considering migrating all company data to the cloud to save money on expensive SAN storage.
Which of the following is a security concern that will MOST likely need to be addressed during migration?
A. Latency
B. Data Exposure
C. Data loss
D. Data dispersion
Correct Answer: B
NEW QUESTION 10:
A company publishes several APIs for customers and is required to use keys to segregate customer data sets.
Which of the following would be the BEST to use to store customer keys?
A. A trusted platform module
B. A hardware security module
C. A localized key store
D. A public key infrastructure
Correct Answer: B
Reference: https://developer.android.com/studio/publish/app-signing
NEW QUESTION 11:
SIMULATION
A product development team has submitted code snippets for review prior to the release of INSTRUCTIONS.
Analyze the code snippets and then select one vulnerability and one fix for each code snippet If at any time you would like to bang back the initial state of the simulation, please click the Reset All button.
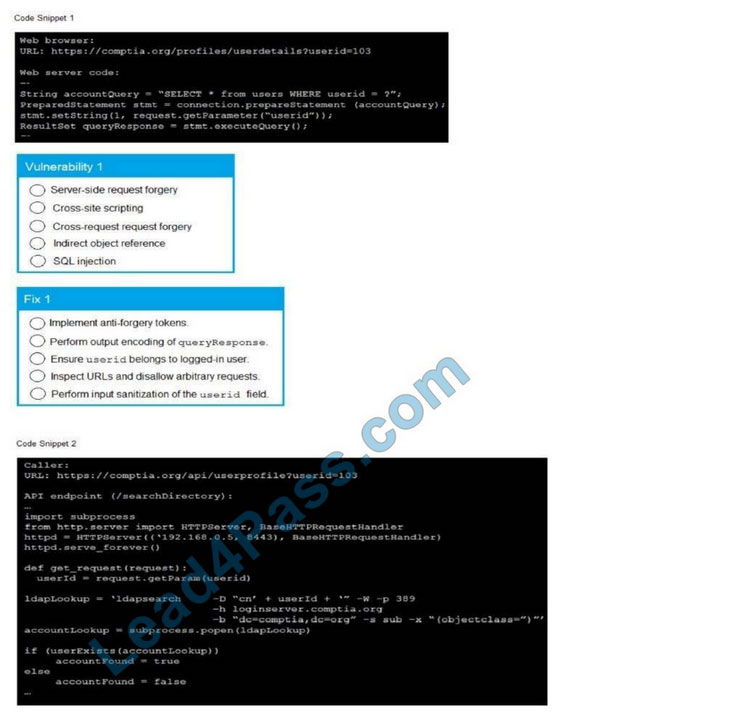
A. Check the answer in the explanation below.
Correct Answer: A
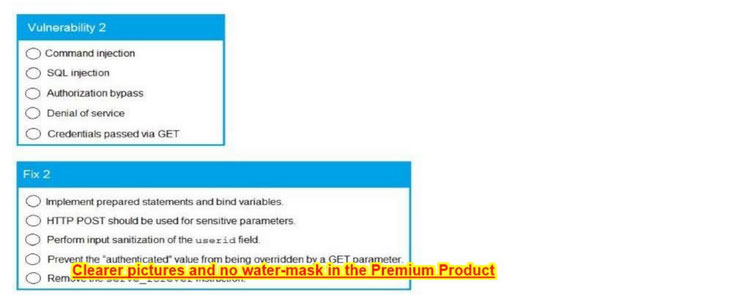
NEW QUESTION 12:
A security auditor needs to review the manner in which an entertainment streaming device operates The auditor is analyzing the output of a port scanning tool to determine the next steps in the security review. Given the following log output:
The best option for the auditor to use NEXT is:
A. a SCAP assessment
B. reverse engineering
C. fuzzing
D. network interception
Correct Answer: A
NEW QUESTION 13:
A company has decided to purchase a license for software that is used to operate a mission-critical process. The third-party developer is new to the industry but is delivering what the company needs at this time.
Which of the following BEST describes the reason why utilizing a source code escrow will reduce the operational risk to the company if the third party stops supporting the application?
A. The company will have access to the latest version to continue development.
B. The company will be able to force the third-party developer to continue support.
C. The company will be able to manage the third-party developer\’s development process.
D. The company will be paid by the third-party developer to hire a new development team.
Correct Answer: A
…
Lead4Pass CAS-004 Dumps contains 406 latest exam questions and answers, one-time use enjoys free updates for 365 days! It also provides PDF and VCE multiple learning formats to assist you in easily learning and passing the CompTIA CAS-004 CASP+ Exam!
Use CompTIA CAS-004 CASP+ Exam Solutions: Download CAS-004 dumps with PDF and VCE: https://www.leads4pass.com/cas-004.html, to help you pass the exam 100% successfully.
[Updated May 2023] Practice the latest CCNP Security 350-701 exam questions online
Lead4Pass updates CCNP Security 350-701 dumps throughout the year, and more importantly, provides some free exam questions each time to help candidates practice their tests online!
May 350-701 dumps have been updated, and verified by the CCNP Security team, as true and effective! Now! Take the newest 350-701 online practice test! also available for download
350-701 dumps with PDF and VCE format: https://www.leads4pass.com/350-701.html (contains 598 latest exam questions and answers!).

CCNP Security 350-701 Exam Questions Online Practice Test:
| From | Number of exam questions | Exam name | Exam code |
| Lead4pass 350-701 dumps | 13 | Implementing and Operating Cisco Security Core Technologies (SCOR) | 350-701 |
QUESTION 1:
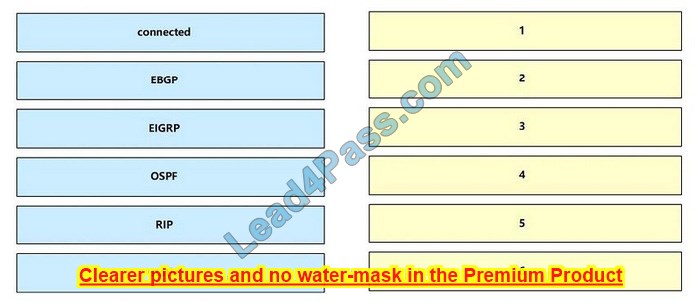
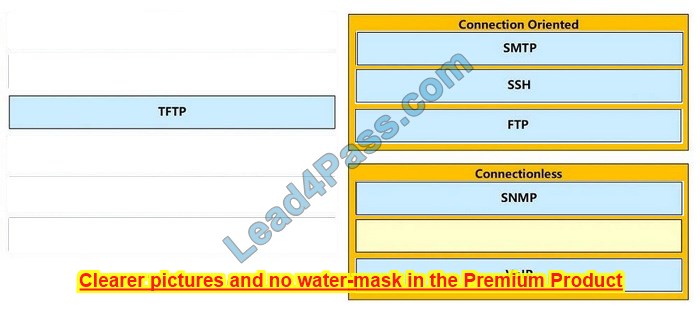
DRAG DROP
Drag and drop the descriptions from the left onto the correct protocol versions on the right.
Select and Place:
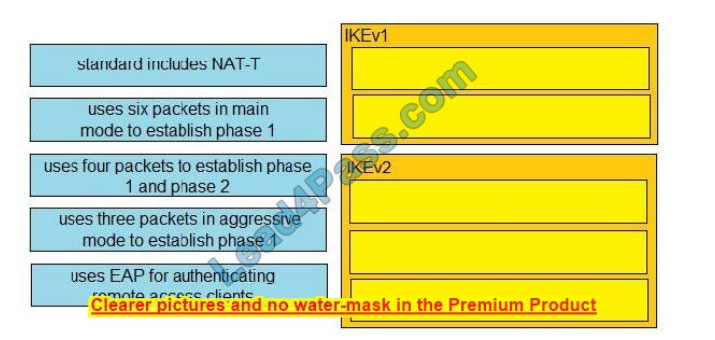
Correct Answer:
QUESTION 2:
Which two risks is a company vulnerable to if it does not have a well-established patching solution for endpoints? (Choose two)
A. exploits
B. ARP spoofing
C. denial-of-service attacks
D. malware
E. eavesdropping
Correct Answer: AD
Malware means “malicious software”, and is any software intentionally designed to cause damage to a computer, server, client, or computer network. The most popular types of malware include viruses, ransomware, and spyware.
Virus Possibly the most common type of malware, viruses attach their malicious code to clean code and wait to be run.
Ransomware is malicious software that infects your computer and displays messages demanding a fee to be paid in order for your system to work again. Spyware is spying software that can secretly record everything you enter, upload, download, and store on your computers or mobile devices. Spyware always tries to keep itself hidden.
An exploit is a code that takes advantage of a software vulnerability or security flaw. Exploits and malware are two risks for endpoints that are not up to date. ARP spoofing and eavesdropping are attacks against the network while denial-of-service attack is based on the flooding of IP packets.
QUESTION 3:
Which endpoint protection and detection feature performs correlation of telemetry, files, and intrusion events that are flagged as possible active breaches?
A. retrospective detection
B. indication of compromise
C. file trajectory
D. elastic search
Correct Answer: B
QUESTION 4:
An organization wants to improve its cybersecurity processes and add intelligence to its data The organization wants to utilize the most current intelligence data for URL filtering, reputations, and vulnerability information that can be integrated with the Cisco FTD and Cisco WSA What must be done to accomplish these objectives?
A. Create a Cisco pxGrid connection to NIST to import this information into the security products for policy use
B. Create an automated download of the Internet Storm Center intelligence feed into the Cisco FTD and Cisco WSA databases to tie to the dynamic access control policies.
C. Download the threat intelligence feed from the IETF and import it into the Cisco FTD and Cisco WSA databases
D. Configure the integrations with Talos Intelligence to take advantage of the threat intelligence that it provides.
Correct Answer: D
QUESTION 5:
Which two are valid suppression types on a Cisco Next-Generation Intrusion Prevention System? (Choose two)
A. Port
B. Rule
C. Source
D. Application
E. Protocol
Correct Answer: BC
QUESTION 6:
The Cisco ASA must support TLS proxy for encrypted Cisco Unified Communications traffic. Where must the ASA be added on the Cisco UC Manager platform?
A. Certificate Trust List
B. Endpoint Trust List
C. Enterprise Proxy Service
D. Secured Collaboration Proxy
Correct Answer: A
QUESTION 7:
Which threat involves software being used to gain unauthorized access to a computer system?
A. virus
B. NTP amplification
C. ping of death
D. HTTP flood
Correct Answer: A
QUESTION 8:
Which type of protection encrypts RSA keys when they are exported and imported?
A. file
B. passphrase
C. NGE
D. nonexportable
Correct Answer: B
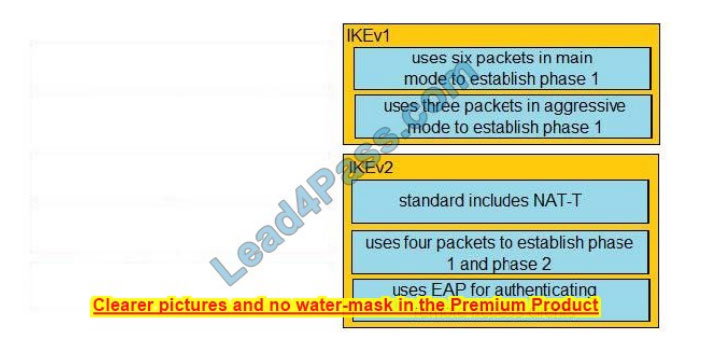
QUESTION 9:
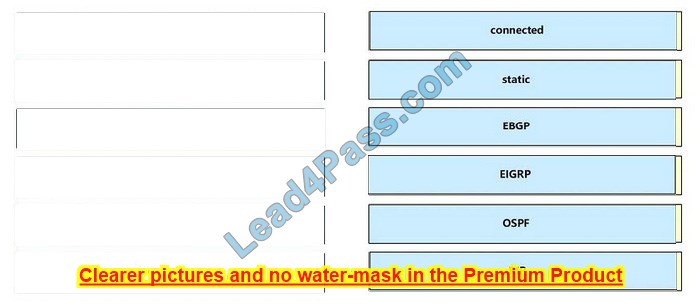
Drag and drop the exploits from the left onto the type of security vulnerability on the right.
Select and Place:
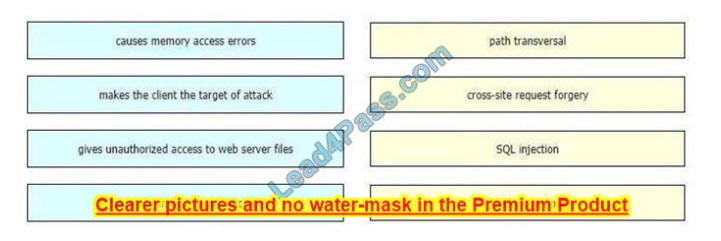
Correct Answer:
QUESTION 10:
An administrator wants to ensure that all endpoints are compliant before users are allowed access to the corporate network.
The endpoints must have the corporate antivirus application installed and be running the latest build of Windows 10.
What must the administrator implement to ensure that all devices are compliant before they are allowed on the network?
A. Cisco Identity Services Engine and AnyConnect Posture module
B. Cisco Stealthwatch and Cisco Identity Services Engine integration
C. Cisco ASA firewall with Dynamic Access Policies configured
D. Cisco Identity Services Engine with PxGrid services enabled
Correct Answer: A
QUESTION 11:
Which IPS engine detects ARP spoofing?
A. Atomic ARP Engine
B. Service Generic Engine
C. ARP Inspection Engine
D. AIC Engine
Correct Answer: A
QUESTION 12:
What is the term for having information about threats and threat actors that helps mitigate harmful events that would otherwise compromise networks or systems?
A. trusted automated exchange
B. Indicators of Compromise
C. The Exploit Database
D. threat intelligence
Correct Answer: D
QUESTION 13:
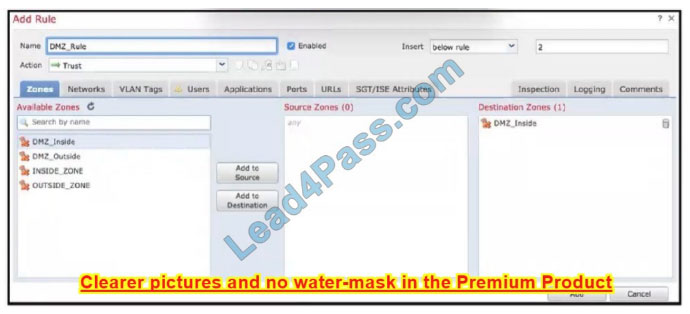
Refer to the exhibit When configuring this access control rule in Cisco FMC, what happens with the traffic destined to the DMZjnside zone once the configuration is deployed?
A. All traffic from any zone to the DMZ_inside zone will be permitted with no further inspection
B. No traffic will be allowed through to the DMZ_inside zone regardless of if it\’s trusted or not
C. All traffic from any zone will be allowed to the DMZ_inside zone only after inspection
D. No traffic will be allowed through to the DMZ_inside zone unless it\’s already trusted
Correct Answer: A
…

PS. Download the latest CCNP Security 350-701 exam practice questions online: https://drive.google.com/file/d/1CK6JCeH42AuFAKJ2TV5g8LRor8ATDFi8/
Every free sharing of CCNP Security 350-701 exam questions is the hard work of our CCNP Security team, and we hope to help you improve your strength!
Now, use 350-701 PDF dumps or 350-701 VCE dumps: https://www.leads4pass.com/350-701.html (both formats contain the latest exam questions and answers!)Also, get 15% off with code “Cisco”!
Practice for the 350-901 DEVCOR exam with newly updated 350-901 dumps
The newly updated 350-901 dumps contain 359 of the latest exam questions and answers, and are available in two practice formats: 350-901 dumps PDF, and 350-901 dumps VCE, to help candidates practice for the exam!
Therefore, downloading 350-901 dumps with PDF and VCE: https://www.leads4pass.com/350-901.html 100% can help candidates pass the 350-901 DEVCOR exam easily and successfully!
What’s more! Part of the Cisco 350-901 dumps exam questions online for free download: https://drive.google.com/file/d/1Z66Uo5DSzTgNfyh3YiTWCd-T9I2f2Xwz/
And you can experience the 350-901 dumps exam practice questions online:
| From | Number of exam questions | Exam name | Exam code | Last updated |
| Lead4Pass | 15 | Developing Applications Using Cisco Core Platforms and APIs (DEVCOR) | 350-901 | 350-901 dumps |
Question 1:
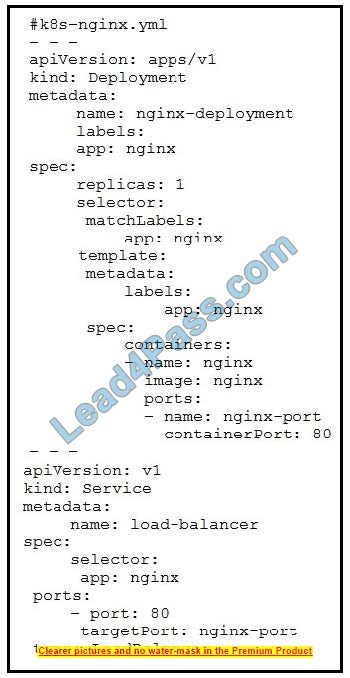
Refer to the exhibit. The presented application consists of an Nginx container and a load balancer service. Which GitLab CI/CD configuration implements the Kubernetes deployment?
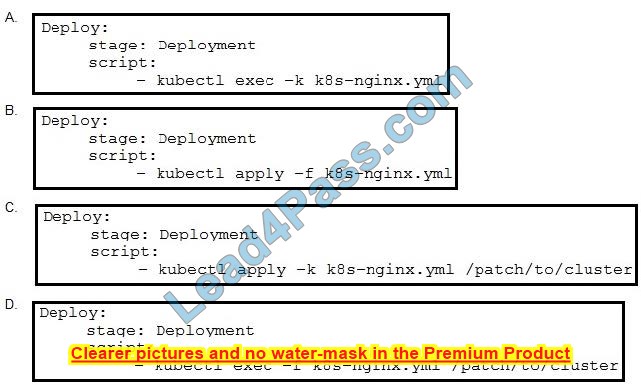
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: B
Explanation: https://kubernetes.io/docs/reference/kubectl/kubectl/
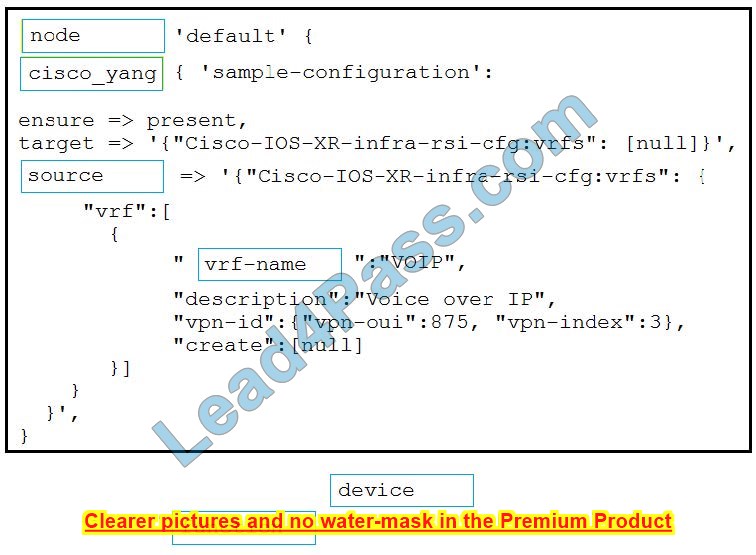
Question 2:
DRAG DROP
Drag and drop the code from the bottom of the code snippet to the blanks in the code to construct a Puppet manifest that configures a VRF instance on a Cisco IOS XR device. Not all options are used.
Select and Place:
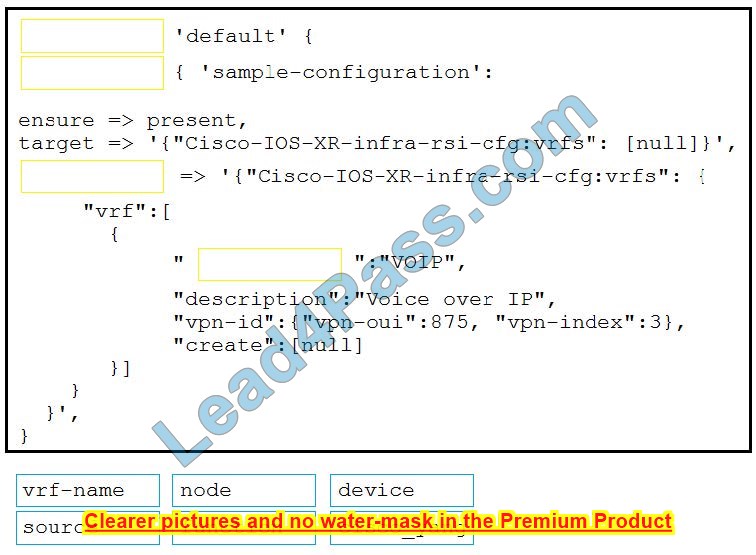
Correct Answer:
Question 3:
Where must the data be encrypted to ensure end-to-end encryption when using an API?
A. on the device that consumes the API
B. on the source device before transmission
C. on the end device after a request is received
D. on the server that stores the data
Correct Answer: A
Question 4:
Which two design considerations should be considered when building a Cisco Meraki dashboard out of available APIs? (Choose two,)
A. API call volume is rate-limited to five calls per second per organization.
B. The API version does not need to be specified in the URL.
C. Access to the API must first be enabled by using the settings for an organization.
D. The API requests require the key and the user credentials.
E. If the API key is shared, it cannot be regenerated
Correct Answer: BC
Question 5:
What is the result of a successful OAuth2 authorization grant flow?
A. The user has the application rights that correspond to the user\’s role within the application\’s database
B. The application is provided with a token that allows actions on services on the user\’s behalf
C. The user has administrative rights to the application\’s backend services
D. The third-party service is provided with a token that allows actions to be performed
Correct Answer: B
Question 6:
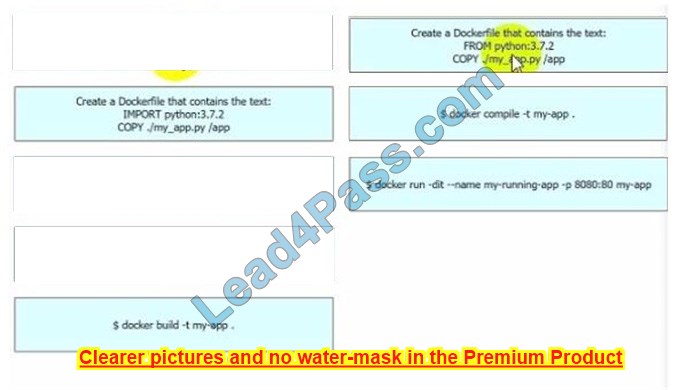
DRAG DROP
Drag and drop the steps from the left into the order on the right to build and run a customized Python Docker image. Not all options are used.
Select and Place:
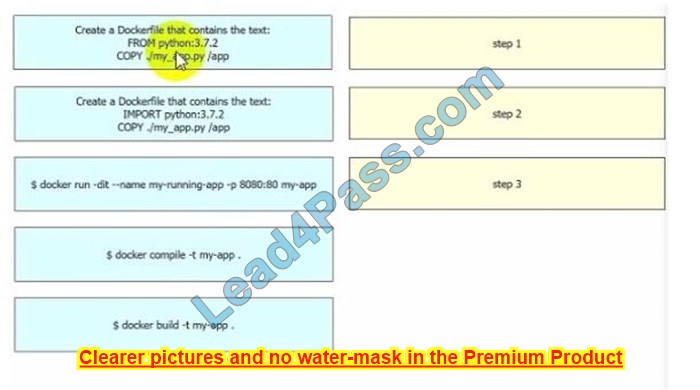
Correct Answer:
Question 7:
Refer to the exhibit. A developer wants to automatically deploy infrastructure for a containerized application. A .gitlab-ci.yml file must describe a pipeline that builds a container based on a supplied Dockerfile and executes an Ansible playbook on the configured container. What must be added where the code S missing to complete the script?
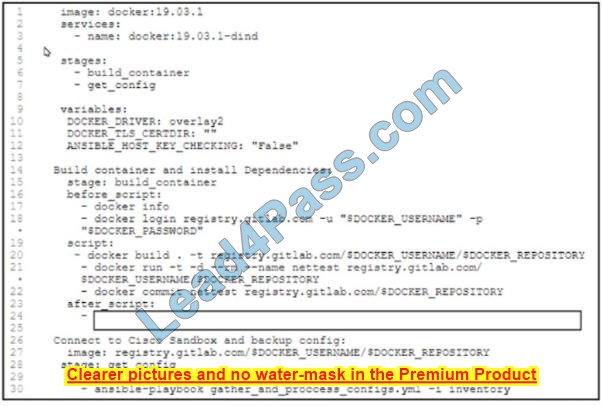
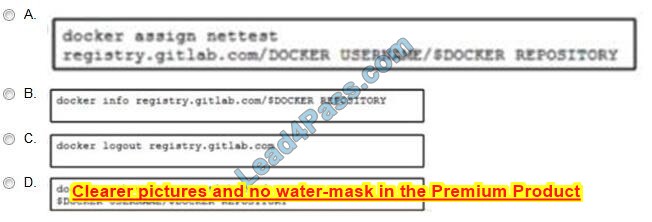
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: D
Question 8:
Which configuration step must be performed on a Cisco IOS XE device to present collected data in Cisco DNA Center?
A. Create an SNMPv3 user account.
B. Apply a telemetry profile.
C. Synchronize the device and the data collector.
D. Enable Cisco NetFlow collection.
Correct Answer: B
Question 9:
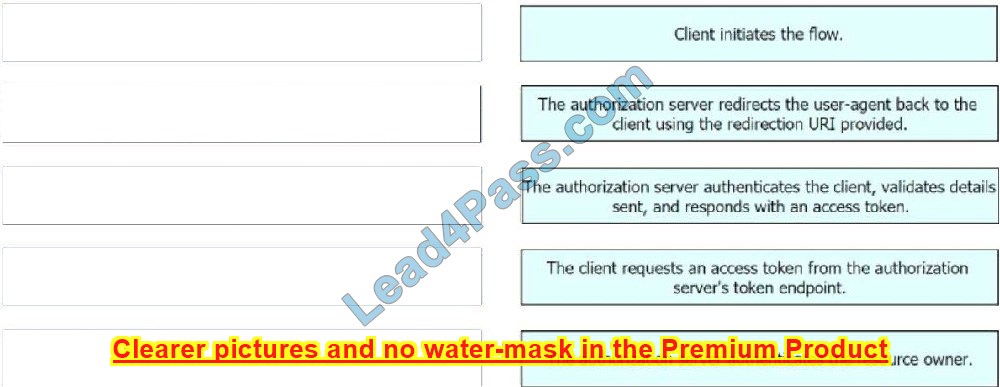
DRAG DROP
Drag and drop the steps from the left into the order of operation on the right for a successful OAuth2 three-legged authorization code grant flow,
Select and Place:
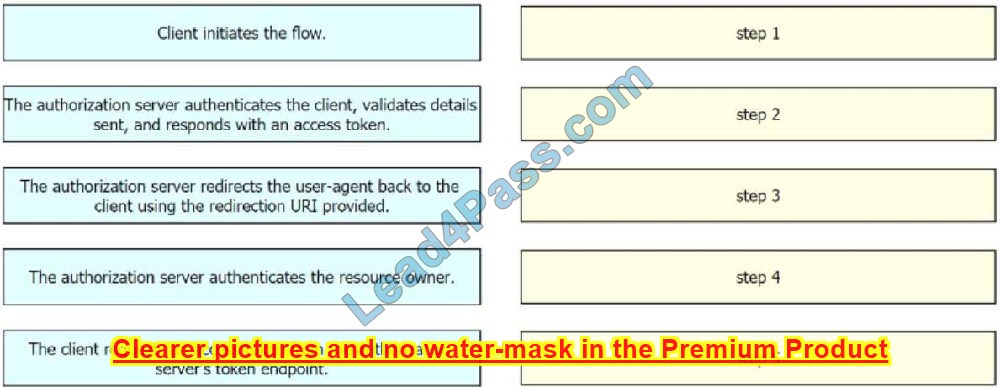
Correct Answer:
Question 10:
A developer creates an application for a Cisco Catalyst 9000 switch in a Docker container. Which action must be taken to host the application on the switch?
A. Copy the application code to a NETCONF file and upload the file to the switch
B. Connect the switch to Cisco DNA Center and push the application through the platform.
C. Use the Cisco IOxClient tool to export the application to a ZIP file and push the file to the switch
D. Export the application as a TAR file and import the file to the switch
Correct Answer: D
Question 11:
DRAG DROP
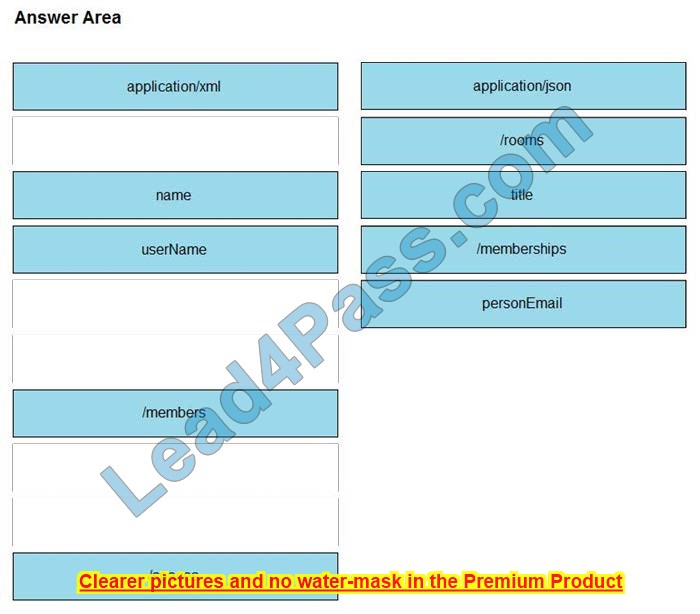
Refer to the exhibit above and click on the resource tabs in the top left corner to view resources to help with this question.
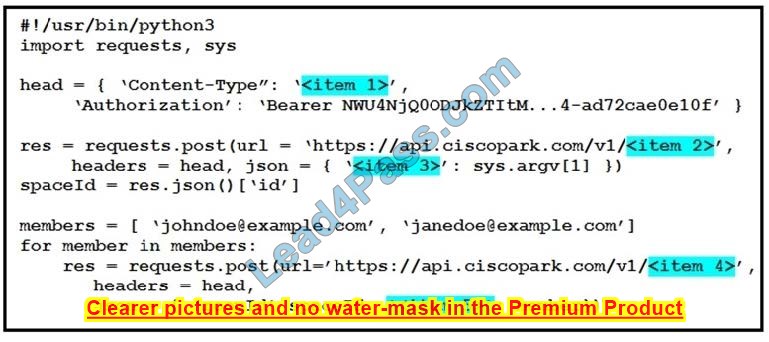
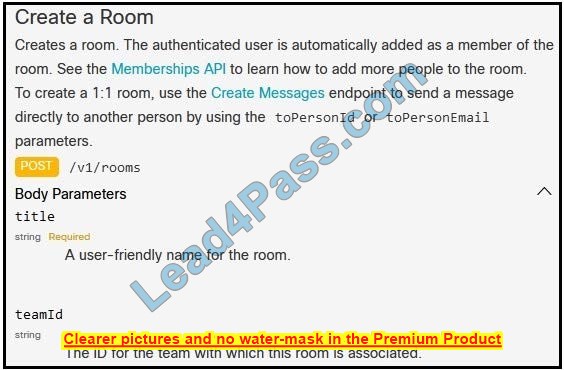
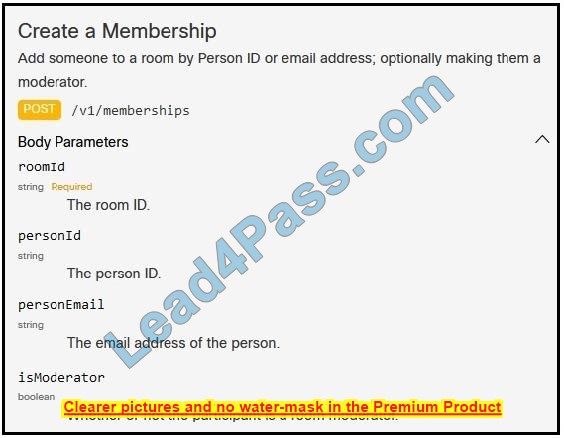
A developer is creating a Python Script that will use the Webex Teams REST API to automatically create a new collaboration space with him and his team leads on-demand via a Linux terminal command. Drag and drop the code snippets from the left onto the numbers on the right that match the missing sections in the exhibit to complete the script. Not all code snippets are used.
Select and Place:
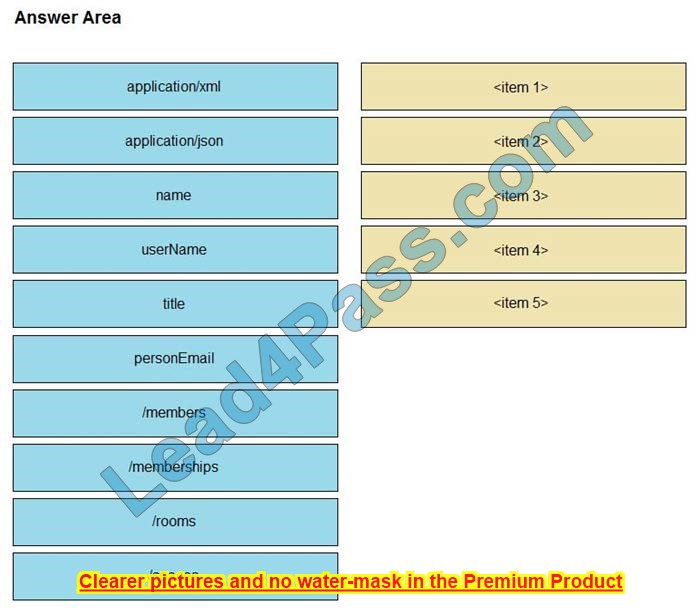
Correct Answer:
Question 12:
Refer to the exhibit.
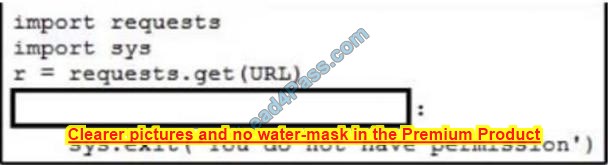
A network engineer needs to handle API errors in their requests when users do not have permission to access the resource, even if they are authenticated and authorized.
Which line of code needs to be placed on the snippet where the code is missing to handle these API errors?
A. if r.status_code == 403
B. il if r.raise for status() == 403
C. if r.raise for_status() = 401
D. if r.status_code = 401
Correct Answer: B
Question 13:
Refer to the exhibit.
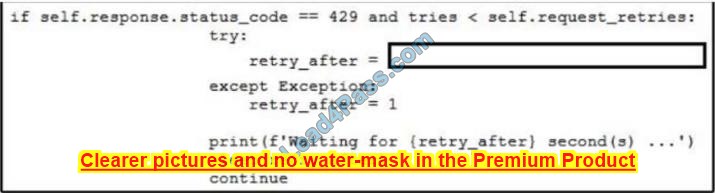
Which line of code needs to be placed on the snippet where the code is missing to provide APl rate-limiting to the requests?
A. int(self.response.headers.post(\’Retry-After\’))
B. int(response.headers.get(\’Retry-After\’))
C. int(self.response.headers.get(Retry-After\’))
D. int(response.headers.post(\’Retry-After\’))
Correct Answer: C
Question 14:
Which scenario is an example of the pseudonymization of sensitive data that meets GDPR requirements?
A. encrypting sensitive data at rest by using native cloud services and data in transit by using SSL/TLS transport
B. implementing XFowarded For at the front of a web app to enable the source IP addresses of headers to change
C. leveraging an application load balancer at the front of a web app for SSL/TLS decryption to inspect data in transit
D. separating the sensitive data into its own dedicated secured data store and using tokens in its place
Correct Answer: A
Question 15:
An application is hosted on Google Kubernetes Engine. A new JavaScript module is created to work with the existing application. Which task is mandatory to make the code ready to deploy?
A. Create a Dockerfile for the code base.
B. Rewrite the code in Python.
C. Build a wrapper for the code to “containerize” it.
D. Rebase the code from the upstream git repo.
Correct Answer: A
…
You only need to practice the 350-901 exam questions carefully to ensure you pass the 350-901 DEVCOR exam successfully!
So download the latest updated 350-901 dumps now: https://www.leads4pass.com/350-901.html (359 Q&A), help you prepare for the 350-901 DEVCOR exam in a very short time and guarantee you 100% successfully passed the exam
best plans for CCNA 200-301 certification exam in 2023

Are you still troubled by the Cisco CCNA 2023 certification exam 2023? You need to develop the most perfect pass exam plan to help you save more time and successfully pass the CCNA 200-301 certification exam.
I won’t discuss how to register, how to maintain a mentality in the test room, and what to do if you fail, I will tell you to prepare and you will succeed.
CCNA 200-301 Exam Essentials
The CCNA 200-301 exam is an exam based on network fundamentals, security fundamentals… Contains 120 multiple-choice questions. the exam is 120 minutes long. Exam fees range from $300 to $325.
Exam questions are multiple-choice and mock questions. There may also be drag-and-drop and fill-in-the-blank type questions. Exam Passing Score: The passing score for the CCNA 200-301 exam is 825 out of 1000.
Exam Validity: The CCNA 200-301 certification is valid for three years. After three years, candidates must pass the recertification exam to maintain their certification.
Career Opportunities: The CCNA 200-301 certification is widely recognized in the industry, Can lead to job opportunities in networking and related fields, including network administration, network engineering, and network security.
CCNA 200-301 exam format
You can take it at a Pearson VUE test center, or online from your home or office with Pearson VUE’s online proctoring service.

Best Plans for CCNA 200-301 Exam
Practice, practice, practice, you have to practice more to ensure that you successfully pass the CCNA 200-301 certification exam, here Lead4Pass 200-301 dumps: https://www.leads4pass.com/200-301.html provides 1190 really effective Exam practice questions and answers that cover complete topics, as well as explanations of difficult questions, to help you really get started on the exam you’re aiming for.
CCNA 200-301 Labs
You need to know how CCNA 200-301 lab verification candidates configure Cisco routers and switches, Lead4Pass provides complete CCNA 200-301 labs exam practice questions, you can learn by PDF or VCE simulation engine, Then, through actual hands-on operation, it will help you get twice the result with half the effort, and help you master how to configure CCNA experimental values and Cisco commands. By practicing and configuring these topologies, you will easily succeed.
Latest CCNA 200-301 exam practice questions (Include Labs Questions 11):
| Type | Number of exam questions | Exam name | Exam code | Last updated |
| Free | 15 | Implementing and Administering Cisco Solutions (CCNA) | 200-301 | 200-301 dumps |
Question 1:
Which command must you enter to guarantee that an HSRP router with higher priority becomes the HSRP primary router after it is reloaded?
A. standby 10 preempt
B. standby 10 version 1
C. standby 10 priority 150
D. standby 10 version 2
Correct Answer: A
The “preempt” command enables the HSRP router with the highest priority to immediately become the active router.
Question 2:
DRAG DROP
Drag and drop the AAA terms from the left onto the descriptions on the right.
Select and Place:
Correct Answer:
Question 3:
Using direct sequence spread spectrum, which three 2.4-GHz channels are used to limit collisions?
A. 1,6.11
B. 1,5,10
C. 1,2,3
D. 5,6,7
Correct Answer: A
Question 4:
Which state does the switch port move to when PortFast is enabled?
A. forwarding
B. listening
C. blocking
D. learning
Correct Answer: A
Question 5:
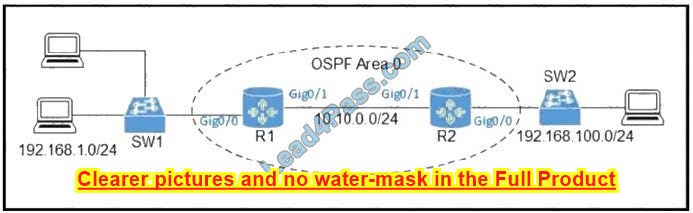
Refer to the exhibit.
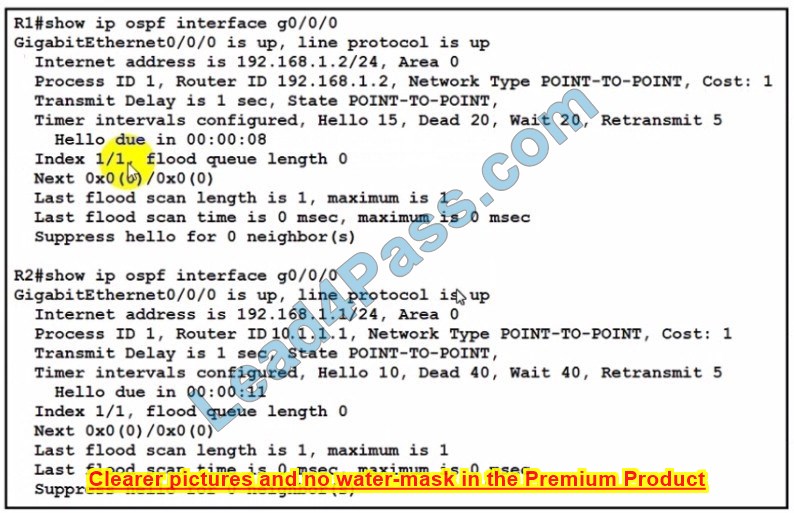
The network engineer is configuring router R2 as a replacement router on the network After the initial configuration is applied it is determined that R2 failed to show R1 as a neighbor. Which configuration must be applied to R2 to complete the OSPF configuration and enable it to establish the neighbor relationship with R1?
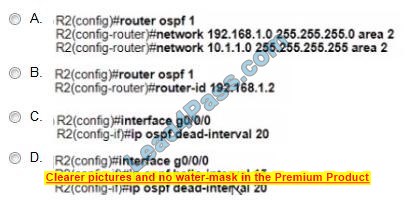
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: D
Question 6:
Refer to the exhibit. Users on existing VLAN 100 can reach sites on the Internet. Which action must the administrator take to establish connectivity to the Internet for users in VLAN 200?
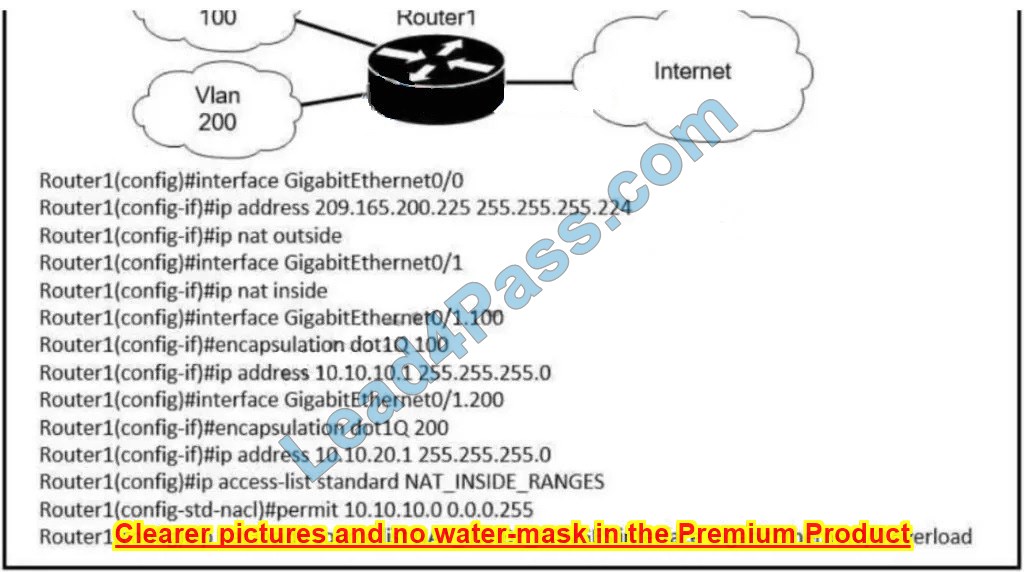
A. Define a NAT pool on the router.
B. Configure static NAT translations for VLAN 200.
C. Configure the ip nat outside command on another interface for VLAN 200.
D. Update the NAT_INSIDE_RANGES ACL
Correct Answer: D
Question 7:
An engineer is installing a new wireless printer with a static IP address on the Wi-Fi network. Which feature must be enabled and configured to prevent connection issues with the printer?
A. client exclusion
B. DHCP address assignment
C. passive client
D. static IP tunneling
Correct Answer: B
Question 8:
What is a feature of TFTP?
A. offers an anonymous user login ability
B. uses two separate connections for control and data traffic
C. relies on the well-known TCP port 20 to transmit data
D. provides secure data transfer
Correct Answer: A
Question 9:
A network engineer is implementing a corporate SSID for WPA3-Personal security with a PSK. Which encryption cipher must be configured?
A. CCMP128
B. GCMP256
C. CCMP256
D. GCMP128
Correct Answer: A
Question 10:
How do traditional campus device management and Cisco DNA Center device management differ in regard to deployment?
A. Traditional campus device management allows a network to scale more quickly than with Cisco DNA Center device management.
B. Cisco DNA Center device management can deploy a network more quickly than traditional campus device management.
C. Cisco DNA Center device management can be implemented at a lower cost than most traditional campus device management options.
D. Traditional campus device management schemes can typically deploy patches and updates more quickly than Cisco DNA Center device management.
Correct Answer: B
Question 11 (CCNA 200-301 labs):
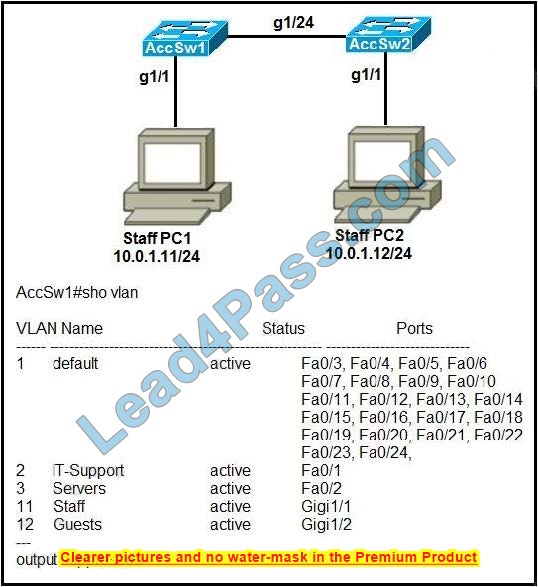
Refer to the exhibit. Switch AccSw1 has just been added to the network along with PC2. All VLANs have been implemented on AccSw2. How must the ports on AccSw2 be configured to establish Layer 2 connectivity between PC1 and PC2?
A. interface GigabitEthernet1/2 switchport mode access switchport access vlan 2
!
interface GigabitEthernet1/24
switchport mode trunk
B. interface GigabitEthernet1/1 switchport mode access switchport access vlan 11
!
interface GigabitEthernet1/24
switchport mode trunk
C. interface GigabitEthernet1/24 switchport mode trunk
switchport trunk allowed vlan 11, 12 ! interface GigabitEthernet1/1
switchport access vlan 11
D. interface GigabitEthernet1/2
switchport mode access
switchport access vlan 12
!
interface GigabitEthernet1/24
switchport mode trunk
switchport trunk allowed vlan 11, 12
Correct Answer: B
Question 12:
How does QoS optimize voice traffic?
A. reducing bandwidth usage
B. by reducing packet loss
C. by differentiating voice and video traffic
D. by increasing jitter
Correct Answer: C
Question 13:
See the below.
A. Check the below
B. Place Holder
C. Place Holder
D. Place Holder
Correct Answer: A
Answer as below configuration:
1.- on R3
config terminal ip route 192.168.1.1 255.255.255.255 209.165.200.229 end copy running start
2.- on R2
config terminal ip route 0.0.0.0 0.0.0.0 209.165.202.130 end copy running start
3.- on R2
config terminal ipv6 route ::/0 2001:db8:abcd::2 end copy running start
Question 14:
DRAG DROP
Drag the IPv6 DNS record types from the left onto the description on the right.
Select and Place:
Correct Answer:
Question 15:
Which device permits or denies network traffic based on a set of rules?
A. access point
B. firewall
C. wireless controller
D. switch
Correct Answer: B
…
Download 1190 200-301 dumps with PDF and VCE: https://www.leads4pass.com/200-301.html (full practice ensures 100% successful pass of CCNA 200-301 exam)
Summarize:
The experience of the successful CCNA 200-301 certification tells the candidates who are about to take the exam: the secret to passing the CCNA 200-301 certification exam is practice. Exams around the world are like this. Only by learning and practicing this knowledge can you You are guaranteed to actually pass the exam. The same is true for the CCNA 200-301 certification exam, use Lead4Pass 200-301 dumps to practice the 1190 exam questions to guarantee your 100% success.
Lead4Pass CCDP 300-910 dumps are the best material for the 300-910 DEVOPS exam
Lead4Pass CCDP 300-910 dumps contain 59 latest exam questions and answers, covering the actual 300-910 DEVOPS exam questions, which is the best material for candidates to take the exam.
This update meets the 2022-2023 300-910 DEVOPS certification exam requirements, use CCDP 300-910 dumps https://www.leads4pass.com/300-910.html, to help you pass the exam successfully on the first attempt.
Read some free CCDP 300-910 exam questions and answers online:
| Number of exam questions | Exam name | Exam code | Last updated |
| 15 | Implementing DevOps Solutions and Practices using Cisco Platforms (DEVOPS) | 300-910 | 300-910 dumps |
Question 1:
Which description of a canary deployment is true?
A. deployment by accident
B. deployment that is rolled back automatically after a configurable amount of minutes
C. deployment relating to data mining development
D. deployment to a limited set of servers or users
Correct Answer: D
Question 2:
The company has experienced serious growth and the hosted applications are getting more and more hits. Based on the increased workload, applications have started to show signs of reduced performance, which is affecting the user experience.
Which two server metrics should be tracked to ensure that the customer experience remains within acceptable limits? (Choose two.)
A. application feature sprawl
B. CPU peak usage
C. CPU average usage
D. microservices count
E. CPU frequency
Correct Answer: BC
Question 3:
Which two practices help make the security of an application a more integral part of the software development lifecycle? (Choose two.)
A. Add a step to the CI/CD pipeline that runs a dynamic code analysis tool during the pipeline execution.
B. Add a step to the CI/CD pipeline that runs a static code analysis tool during the pipeline execution.
C. Use only software modules that are written by the internal team.
D. Add a step to the CI/CD pipeline to modify the release plan so that updated versions of the software are made available more often.
E. Ensure that the code repository server has enabled drive encryption and stores the keys on a Trusted Platform Module or Hardware Security Module.
Correct Answer: AE
Question 4:
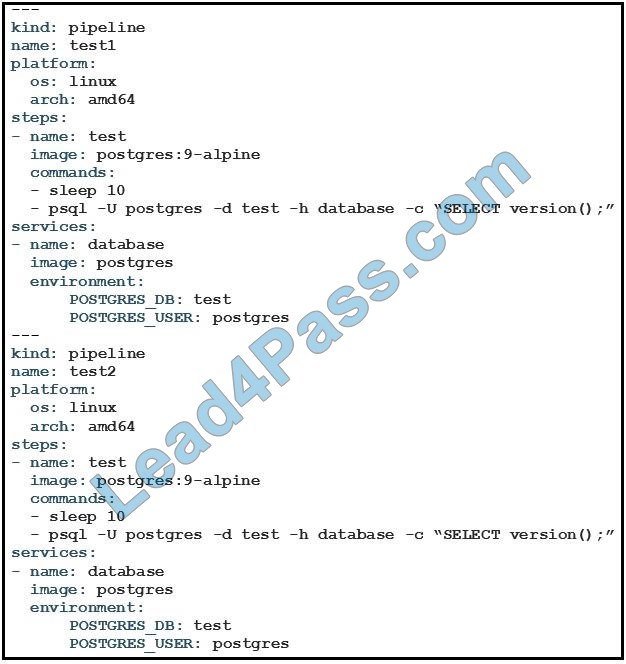
Refer to the exhibit. What is the user doing with Drone in this automated test?
A. testing Alpine Linux versus Ubuntu Linux
B. testing a PostgreSQL DB against multiple architectures
C. testing only the amd64 architecture
D. testing PostgreSQL deployment in an Alpine Linux VM
Correct Answer: D
Question 5:
To make logging searches more efficient and useful in Kibana, an Administrator wants to implement index patterns around the hostname of some software systems. Where should this be configured?
A. Configure a new JSON object in Kibana.
B. Create a search index in Logstash.
C. Create an index pattern in Kibana.
D. Create a time filter on Kibana to look at time only.
Correct Answer: C
Question 6:
What is chaos engineering?
A. designing an application with fuzzy logic that makes it hard to predict
B. a product engineering approach that lacks a formal methodology
C. splitting a project between teams that do not communicate with each other
D. introducing problems into a system to study behavior and improve reliability
Correct Answer: D
Question 7:
Which interface is most commonly used to integrate logging, monitoring, and alerting applications into your CI/CD pipeline?
A. AMQP
B. SNMP
C. SSH
D. REST
Correct Answer: C
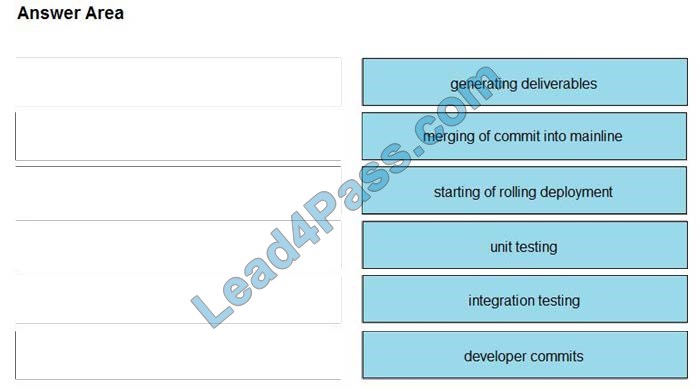
Question 8:
DRAG DROP
Drag and drop the operations from the left into the correct order on the right when using CI/CD, assuming that there are no failures or conflicts.
Select and Place:
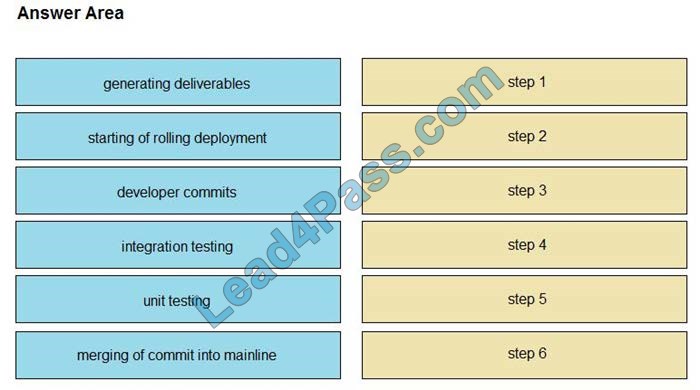
Correct Answer:
Question 9:
DevOps engineering wants to build an application implementation based on the CI/CD pipeline model. Which service should be used to provide hosted continuous service for open and private projects?
A. Ansible
B. pyATS
C. Genie CLI
D. Travis CI
Correct Answer: D
Question 10:
A user wants to deploy a new service to a Kubernetes cluster. Which two commands accomplish this goal? (Choose two.)
A. Apply
B. Install
C. Deploy
D. Create
E. Expose
Correct Answer: AE
Question 11:
What are the two advantages of using Configuration Management Tools? (Choose two.)
A. reduction in policy violations caused by human errors
B. reduction in administration costs
C. reduction in the network changes already performed automatically
D. reduction of on-premises networking equipment
E. reduction in networking team skills
Correct Answer: BC
Question 12:
When DevOps practices are integrated into an existing organization, which two characteristics are positive indicators of DevOps maturity? (Choose two.)
A. mean time between success
B. mean time to recover
C. cone testing
D. change lead time
E. age of codebase
Correct Answer: BD
Question 13:
Which two elements help to secure your API keys? (Choose two.)
A. ramdomness
B. SHA1
C. triple AES
D. rotation
E. dictionary
Correct Answer: AC
Question 14:
Which type of testing should be integrated into a CI/CD pipeline to ensure the correct behavior of all of the modules in the source code that were developed using TDD?
A. soak testing
B. unit testing
C. load testing
D. volume testing
Correct Answer: B
Question 15:
How long do analysis systems such as Elasticsearch, Logstash, and Kibana Stack handle ingesting unstructured logs from different devices in various formats?
A. All devices that generate Syslog must use agents that process the local logs and transmit them in a specific format to the ELK Stack.
B. All logs are stored in their unstructured text format, and the ELK Stack performs data analysis by intelligently parsing the logs using machine learning algorithms.
C. All different message formats are parsed separately using custom filters, and the resulting structured data is stored for later analysis.
D. A single, comprehensive log format is defined on the ELK Stack. All incoming logs, regardless of format, are transformed to match the comprehensive format, and only applicable fields are populated.
Correct Answer: D
…
Lead4Pass CCDP 300-910 dumps: https://www.leads4pass.com/300-910.html (59 Q&A) Reviewed by a professional team is the best material for the 300-910 DEVOPS exam.
Get Live update CCNP Enterprise 350-401 dumps with PDF and VCE

Live update CCNP Enterprise 350-401 dumps with PDF and VCE from Lead4Pass, get real valid 350-401 dumps https://www.leads4pass.com/350-401.html (866 Q&A).
Provide 365 days of free updates and online customer service to ensure that 350-401 ENCOR exam candidates save more costs and pass the exam successfully.
And, provide a part of Lead4Pass 350-401 dumps PDF online download: https://drive.google.com/file/d/14FtbIb6_G2tGECN_fvyVIxB7I8VqpH8r/
Read free CCNP Enterprise 350-401 dumps exam questions and answers online:
New Question 1:
If a client\’s radio device receives a signal strength of -67 dBm and the noise floor is -85 dBm, what is the SNR value?
A. 15 dB
B. 16 dB
C. 18 dB
D. 20 dB
Correct Answer: C
New Question 2:
Refer to the exhibit.
An engineer must allow R1 to advertise the 192 168.1 0/24 network to R2 R1 must perform this action without sending OSPF packets to SW1 Which command set should be applied?

A. Option A
B. Option B
C. Option C
Correct Answer: B
New Question 3:
Which method creates an EEM applet policy that is registered with EEM and runs on demand or manually?
A. event manager applet OnDemand event register action 1.0 Syslog priority critical msg \’ This is a message from ondemand\’
B. event manager applet OnDemand event manual action 1.0 Syslog priority critical msg \’This is a message from ondemand\’
C. event manager applet OnDemand event none action 1.0 Syslog priority critical msg \’This is a message from ondemand\’
D. event manager applet ondemand action 1.0 Syslog priority critical msg \’ This is a message from ondemand\’
Correct Answer: C
An EEM policy is an entity that defines an event and the actions to be taken when that event occurs. There are two types of EEM policies: an applet or a script.
An applet is a simple form of policy that is defined within the CLI configuration. answer \’ event manager applet OnDemand event register action 1.0 Syslog priority critical msg `This is a message from ondemand\’ <=” p=” style=”box-sizing: border-box;”> There are two ways to manually run an EEM policy.
EEM usually schedules and runs policies on the basis of an event specification that is contained within the policy itself.
The event no command allows EEM to identify an EEM policy that can be manually triggered.
To run the policy, use either the action policy command in applet configuration mode or the event manager run command in privileged EXEC mode.
New Question 4:
Which action is performed by Link Management Protocol In a Cisco StackWise Virtual domain?
A. it determines if the hardware Is compatible to form the StackWise Virtual domain.
B. It determines which switch becomes active or standby.
C. It discovers the StackWise domain and brings up SVL interfaces.
D. It rejects any unidirectional link traffic forwarding.
Correct Answer: B
The Link Management Protocol (LMP) performs the following functions: + Verifies link integrity by establishing bidirectional traffic forwarding, and rejects any unidirectional links + Exchanges periodic hellos to monitor and maintain the health of the links + Negotiates the version of StackWise Virtual header between the switches StackWise Virtual link role resolution
New Question 5:
A Cisco DNA Center REST API sends a PUT to the /DNA/intent/API/v1/network-device endpoint A response code of 504 is received What does the code indicate?
A. The response timed out based on a configured interval
B. The user does not have the authorization to access this endpoint.
C. The username and password are not correct
D. The web server is not available
Correct Answer: A
New Question 6:
Refer to the exhibit.
Which command set is needed to configure and verify router R3 to measure the response time from router R3 to the file server located in the data center?
A. IP SLA 6 ICMP-echo 10.0.1.3 source-IP 10.0.0.3
frequency 300
IP SLA schedule 6 life forever start-time now
show IP SLA statistics 6
B. IP SLA 6 ICMP-echo 172.29.139.134 source-IP 172.29.139.132 frequency 300 ip sla schedule 6 start-time now
C. IP SLA 6 ICMP-echo 172.29.139.134 source-IP 172.29.139.132 frequency 300 ip sla schedule 6 Start-time now shows IP protocol
D. IP SLA 6 ICMP-echo 10.0.1.3 source-IP 10.0.0.3 frequency 300 ip sla schedule 6 life forever start-time now show IP protocol
Correct Answer: A
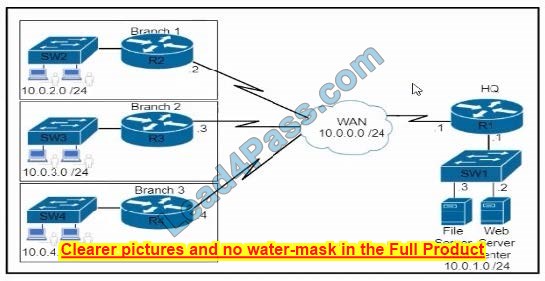
New Question 7:
Refer to the exhibit. An engineer must permit traffic from these networks and block all other traffic An informational log message should be triggered when traffic enters from these prefixes Which access list must be used?
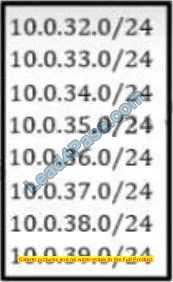
A. access-list acl_subnets permit IP 10.0.32.0 0 0.0.255 log
B. access-list acl_subn*ls permit IP 10.0.32.0 0.0.7.255 log
C. access-list acl_subnets permit IP 10.0.32.0 0.0.7.255 access-list acl_subnets deny IP any log
D. access-list acl_subnets permit IP 10.0.32.0 255.255.248.0 log
Correct Answer: B
New Question 8:
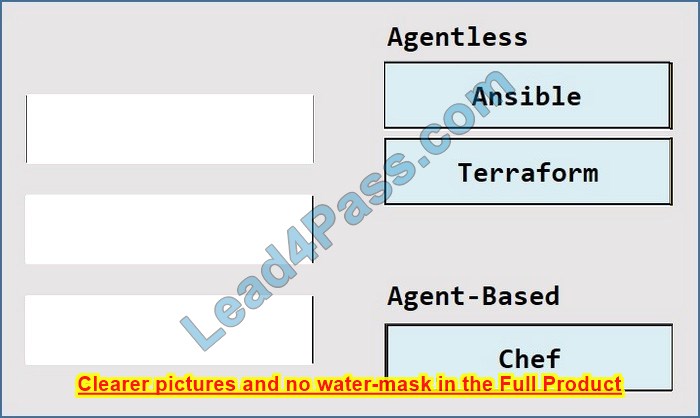
DRAG DROP
Drag and drop the tools from the left onto the agent types on the right.
Select and Place:
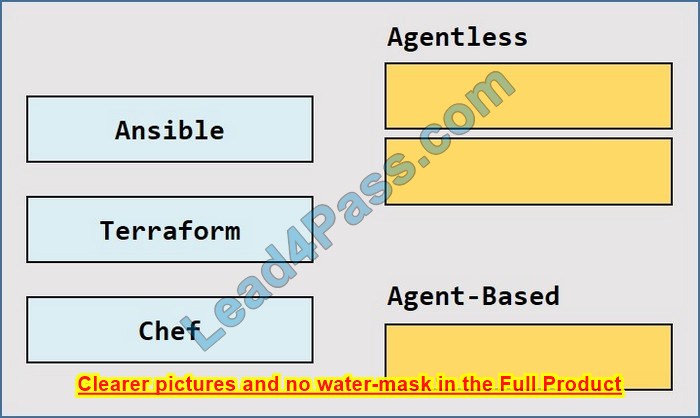
Correct Answer:
New Question 9:
Which method should an engineer use to deal with a long-standing contention issue between any two VMs on the same host?
A. Adjust the resource reservation limits
B. Live migrate the VM to another host
C. Reset the VM
D. Reset the host
Correct Answer: A
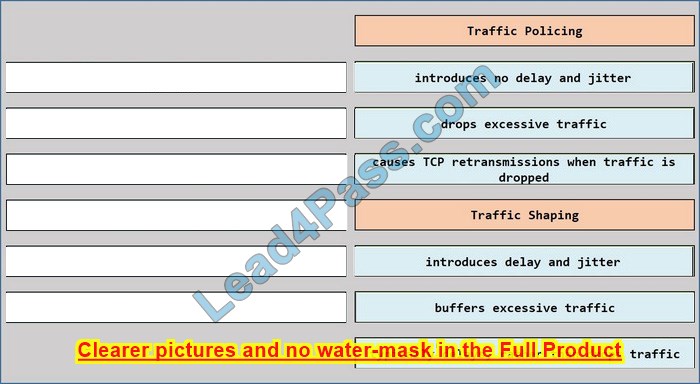
New Question 10:
DRAG DROP
Drag and drop the descriptions from the left onto the QoS components on the right.
Select and Place:
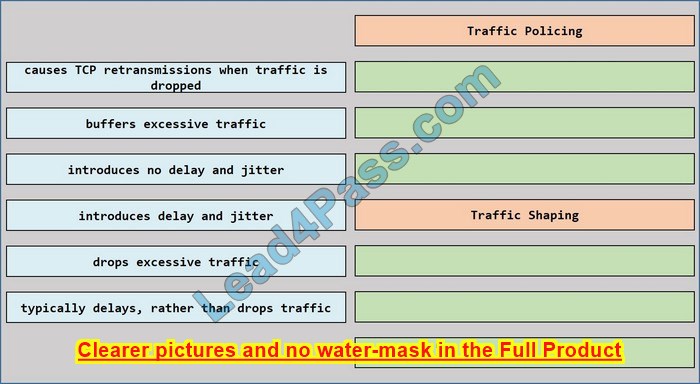
Correct Answer:
New Question 11:
Which access point mode allows a supported AP to function like a WLAN client would, associating and identifying client connectivity issues?
A. client mode
B. SE-connect mode
C. sensor mode
D. sniffer mode
Correct Answer: C
As these wireless networks grow especially in remote facilities where IT professionals may not always be on-site, it becomes even more important to be able to quickly identify and resolve potential connectivity issues ideally before the users complain or notice connectivity degradation.
To address these issues we have created Cisco\’s Wireless Service Assurance and a new AP mode called “sensor” mode.
Cisco\’s Wireless Service Assurance platform has three components, namely, Wireless PerformanceAnalytics, Real-time Client Troubleshooting, and Proactive Health Assessment.
Using a supported AP-ordedicated sensor the device can actually function much like a WLAN client would associating and identifying client connectivity issues within the network in real time without requiring an IT or technician to be on site.
New Question 12:
What is the function of a fabric border node in a Cisco SD-Access environment?
A. To collect traffic flow information toward external networks
B. To connect the Cisco SD-Access fabric to another fabric or external Layer 3 networks
C. To attach and register clients to the fabric
D. To handle an ordered list of IP addresses and locations for endpoints in the fabric.
Correct Answer: B
New Question 13:
Which element enables the communication between guest VMs within a virtualized environment?
A. hypervisor
B. vSwitch
C. virtual router
D. pNIC
Correct Answer: B
Each VM is provided with a virtual NIC (vNIC) that is connected to the virtual switch. Multiple NICs can connect to a single vSwitch, allowing VMs on a physical host to communicate with one another at layer 2 without having to go out to a physical switch.
New Question 14:
Which two statements about Cisco Express Forwarding load balancing are true? (Choose two)
A. Each hash maps directly to a single entry in the RIB
B. It combines the source IP address subnet mask to create a hash for each destination
C. Cisco Express Forwarding can load-balance over a maximum of two destinations
D. It combines the source and destination IP addresses to create a hash for each destination
E. Each hash maps directly to a single entry in the adjacency table
Correct Answer: DE
Cisco IOS software basically supports two modes of CEF load balancing: On a per-destination or perpacket basis.
For per-destination load balancing a hash is computed out of the source and destination IP address (-> Answer \’ It combines the source and destination IP addresses to create a hash for each destination\’ is correct).
This hash points to exactly one of the adjacency entries in the adjacency table (-> Answer \’ Each hash maps directly to a single entry in the adjacency table\’ is correct), providing that the same path is used for all packets with this source/destination address pair.
If per-packet load balancing is used the packets are distributed round-robin over the available paths. In either case, the information in the FIB and adjacency tables provide all the necessary forwarding information, just like for non-load balancing operations.
The number of paths used is limited by the number of entries the routing protocol puts in the routing table, the default in IOS is 4 entries for most IP routing protocols with the exception of BGP, where it is one entry.
The maximum number that can be configured in 6 different paths -> Answer \’ Cisco Express Forwarding can load-balance over a maximum of two destinations\’ is not correct.
New Question 15:
If a VRRP master router fails, which router is selected as the new master router?
A. a router with the highest priority
B. a router with the highest loopback address
C. a router with the lowest loopback address
D. router with the lowest priority
Correct Answer: A
…
Select 350-401 dumps of Lead4Pass real-time updates: https://www.leads4pass.com/350-401.html (PDF + VCE), Helping you successfully pass the 350-401 ENCOR exam.
BTW, Download More Free CCNP Enterprise 350-401 Dumps Exam Questions:
https://drive.google.com/file/d/14FtbIb6_G2tGECN_fvyVIxB7I8VqpH8r/
https://drive.google.com/file/d/1ahrnRyvF4ubbTamp6ejufmuvDDV3xA_H/
https://drive.google.com/file/d/1CzUD7IShCoh1JNUYek2Q2REVIzJprjMs/
https://drive.google.com/file/d/1UZ1OCWXuClKs73-SDQXFO8j-oA4A8a8Q/
https://drive.google.com/file/d/1fYt1qLwW_w51z4Gr4pUOqVnyab6Ioeg3/
CCNP Collaboration exam dumps sharing from Lead4Pass
Learn about the CCNP Collaboration certification exam:
- What is CCNP Collaboration Certification
- What are CCNP Collaboration exam dumps
- Is CCNP Collaboration Certification Valuable
- How to Get CCNP Collaboration Certification
- CCNP Collaboration 300-815 CLACCM Exam Question Examples
- Summarize
What is CCNP Collaboration Certification?
If you are a big fan of Cisco certification, then you must know the importance of Cisco certification. Cisco has changed a lot since 2020. If you don’t know it yet, you can check out an article I published in 2020 about Cisco changing 2020, This article I am in 2022 A new update has also been made in the year, and I believe it will help you.
CCNP Collaboration certification is a new certification program after 2020. It has replaced some old exam items and added new items.
All in all, the CCNP Collaboration certification is divided into two parts: one is the core exam and the other is the concentration exam, but to get the CCNP Collaboration certification you first need to get the core exam (350-801 CLCOR) and then choose according to your needs and interests
A centralized exam program of your choice, each exam is certified by an individual expert, so your accomplishments along the way are recognized.
What are CCNP Collaboration exam dumps?
First of all, let me talk about what is Exam dumps, Brain dumps, or simply Dumps. Exam Dumps is a long-tail word for exam materials, which stands for the abbreviation of two format files (PDF file and VCE exam engine).
Many candidates need to take multiple certification exams in a short period of time, and it is conceivable that this is difficult, so Exam Dumps appeared, which helps candidates to learn quickly, improve their study plan and exam focus, and help candidates to be able to More confident to stand out successfully.
CCNP Collaboration exam dumps contain core exam content and focused exam content:
350-801 exam dumps (core exam): https://www.leads4pass.com/350-801.html
300-810 exam dumps
300-815 exam dumps
300-820 exam dumps
300-825 exam dumps
300-830 exam dumps
300-835 exam dumps
Is CCNP Collaboration Certification Valuable?
At the beginning of 2020, great changes have taken place in the world. I believe everyone knows that it is about everyone. This is not the focus of our expression, but it is related to our lives. So what kind of work is the most enviable in this era? Become a doctor, a teacher, a soldier, a lawyer,
Or other… These are all good careers, but I recommend getting a certification in an industry that helps us resist risks, increase income, and improve our living standards, which is the greatest value.
Cisco certification is a popular certification in the industry, and there are countless participants, which also shows its value. CCNP Collaboration certification is a large branch of Cisco certification and is a very popular certification program, and success in any of them It will help you improve your own value.
How to Get CCNP Collaboration Certification?
Candidates who want to get CCNP Collaboration certification must take the CCNP Collaboration certification exam, as I said above, you need to pass the core exam (350-801 CLCOR), and then select some of the focused exam items you are interested in:
300-810 CLICA Implementing Cisco Collaboration Applications (CLICA)
300-815 CLACCM Implementing Cisco Advanced Call Control and Mobility Services (CLACCM)
300-820 CLCEI Implementing Cisco Collaboration Cloud and Edge Solutions (CLCEI)
300-825 CLCNF Implementing Cisco Collaboration Conferencing (CLCNF)
300-835 CLAUTO Implementing Automation for Cisco Collaboration Solutions (CLAUI)
If you have enough time to prepare for an exam, then you should study hard, refer to online materials, then take the exam with full energy and pray for success.
I have introduced CCNP Collaboration Exam dumps above, it is suitable for candidates of any learning situation, candidates can seriously practice all exam questions and answers provided by Lead4Pass and can guarantee 100% passing the exam.
CCNP Collaboration 300-815 CLACCM Exam Question Example:
I share 300-815 CLACCM exam questions to help you understand the exam dump provided by Lead4pass.
NEW QUESTION 1:
An administrator is asked to configure egress call routing by applying globalization and localization on Cisco UCM.
How should this be accomplished?
A. Localize the calling and called numbers to E.164 format and globalize the called number in the gateway.
B. Globalize the calling and called numbers to E.164 format and localize the called number in the gateway.
C. Localize the calling and called numbers to PSTN format and globalize the calling and called numbers in the gateway.
D. Globalize the calling and called numbers to PSTN format and localize the calling number in the gateway.
Correct Answer: B
NEW QUESTION 2:
Refer to the exhibit.
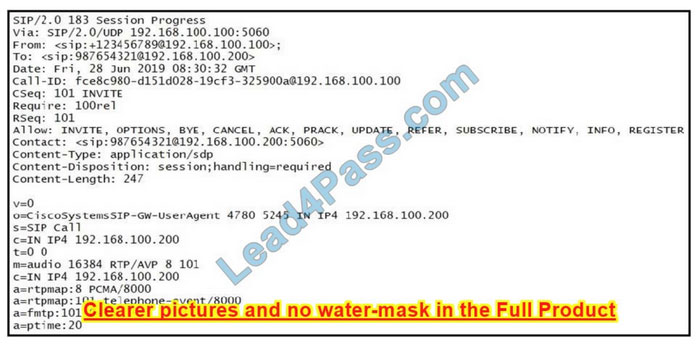
While troubleshooting call failures on the Cisco Unified Border Element, an administrator notices that messages are being sent to the service provider, but there is no response.
The administrator later learns that this SIP provider does not support PRACK.
Which header should be removed from the SIP message to resolve this issue?
A. Require: 100rel
B. Content-Type: application/SDP
C. Contact:
D. Content-Disposition: session;handling=required
Correct Answer: A
NEW QUESTION 3:
What is the first preference condition matched in a SIP-enabled incoming dial peer?
A. incoming uri
B. target carrier-id
C. answer-address
D. incoming called-number
Correct Answer: A
NEW QUESTION 4:
An engineer must configure a Cisco UCM hunt list so that calls to users in a line group are routed to the first idle user and then the next.
Which distribution algorithm must be configured to accomplish this task?
A. broadcast
B. top down
C. longest idle time
D. circular
Correct Answer: B
Reference: https://www.cisco.com/en/US/docs/voice_ip_comm/cucm/admin/4_0_1/ccmcfg/b03lngrp.html
NEW QUESTION 5:
An engineer must implement call restrictions to toll-free numbers using a class of restrictions in a branch of Cisco UCME.
In which two places is the coolest incoming or cor incoming command configured? (Choose two.)
A. “voice register pool ” configuration mode
B. “ephone-dn ” configuration mode
C. “dial-peer cor custom ” configuration mode
D. “voice register global ” configuration mode
E. “telephony-service ” configuration mode
Correct Answer: AB
NEW QUESTION 6:
What is a description of RTP timestamps or sequence numbers?
A. The sequence number is used to detect losses.
B. Timestamps increase by the time “carrying” by a packet.
C. Sequence numbers increase by four for each RTP packet transmitted.
D. The timestamp is used to place the incoming audio and video packets in the correct timing order (playout delay compensation).
Correct Answer: D
Reference: https://www.cs.columbia.edu/~hgs/rtp/faq.html
NEW QUESTION 7:
A customer has multisite deployments with a globalized dial plan. The customer wants to route PSTN calls via the gateway assigned to each site.
Which two actions will fulfill the requirement? (Choose two.)
A. Create one global route list for PSTN calls that points to one global PSTN route group.
B. Create a route group that has all the gateways and associate it with the device pool of every site.
C. Assign one route group as a local route group in the device pool of the corresponding site.
D. Create one route group for each site and one global route list for PSTN calls that point to the local route group.
E. Create a hunt group and assign it to each side route pattern.
Correct Answer: CD
Reference: https://www.cisco.com/c/en/us/td/docs/voice_ip_comm/cucm/srnd/8x/uc8x/dialplan.html
NEW QUESTION 8:
Refer to the exhibit.
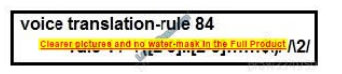
Users report that outbound PSTN calls from phones registered to Cisco UCM are not completed. The local service provider in North America has a requirement to receive calls in a 10-digit format.
The Cisco UCM sends the calls to the Cisco Unified Border Element router in a globalized E.164 format. There is an outbound dial peer on Cisco Unified Border Element configured to send the calls to the provider.
The dial-peer has a voice translation profile applied in the correct direction but an incorrect voice translation rule is applied.
Which rule modifies DNIS in the format that the provider is expecting?
A. rule 1 /^+([^1].*)/ /011\1/
B. rule 1/^+1([2-9]..[2-9]……$)/ /\1/
C. rule 1 /^([2-9]..[2-9]……$)/ /\1/
D. rule 1 /^+1([2-9]..[2-9]……$)/ /\0/
Correct Answer: B
NEW QUESTION 9:
Which two types of distribution algorithms are within a line group? (Choose two.)
A. random
B. circular
C. highest preference
D. top down
E. bottom up
Correct Answer: BD
NEW QUESTION 10:
What are two configuration features of the Standard Local Route Group deployment? (Choose two.)
A. is associated with the route group
B. is associated only with the route list
C. chooses the route group that is configured under the device pool of the calling-party device
D. chooses the route group that is configured under the device pool of the called-party device
E. is assigned directly to the route pattern
Correct Answer: BC
NEW QUESTION 11:
What is the relationship between partition, time schedule, and the time period in Time-of-Day routing in Cisco UCM?
A. A partition can have multiple time schedules assigned. A time schedule contains one or more time periods.
B. A partition can have a one-time schedule assigned. A time schedule contains one or more time periods.
C. A partition can have multiple time schedules assigned. A time schedule contains only one time period.
D. A partition can have a one-time schedule assigned. A time schedule contains only one time period.
Correct Answer: A
NEW QUESTION 12:
Refer to the exhibit.
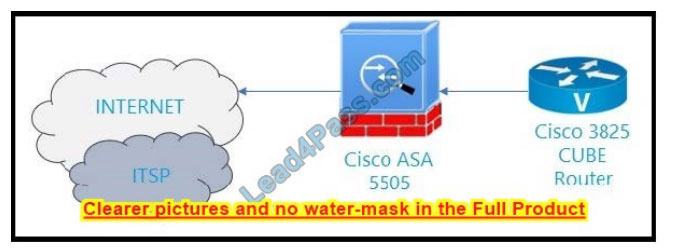
An administrator is troubleshooting a problem in which some outbound calls from an internal network to the Internet telephony service provider are not getting connected, but some others connect successfully.
The firewall team found that some call attempts on port 5060 came from an unrecognized IP that has not been defined in the firewall rule.
What should the administrator configure in the Cisco Unified Border Element to fix this issue?
A. use of port 5061 for SIP secure
B. access list allowing the firewall IP
C. bind signaling and media to the loopback interface
D. IP prefix list to filter the unwanted IP address
Correct Answer: C
NEW QUESTION 13:
Why would RTP traffic that is sent from the originating endpoint fails to be received on the far endpoint?
A. The far-end connection data (c=) in the SDP was overwritten by deep packet inspection in the call signaling path.
B. Cisco UCM invoked media termination point resources.
C. The RTP traffic is arriving beyond the jitter buffer on the receiving end.
D. A firewall in the media path is blocking TCP ports 16384-32768.
Correct Answer: C
…
Download CCNP Collaboration 300-815 CLACCM Exam Questions and Answers:https://drive.google.com/file/d/1jW9EETiUpbWRqfrjNScwp5y7i8c_hiyg/
Candidates are welcome to download CCNP Collaboration 300-815 exam dumps: https://www.leads4pass.com/300-815.html (118 Q&A)
Summarize:
CCNP Collaboration certification is a very popular exam program in 2020 so far, and successfully passing any of them can help candidates improve their quality of life. Candidates can use the CCNP Collaboration certification exam dump provided by Lead4pass Save learning and practice and ensure success rate.
Latest updated CCNP Security 300-725 dumps from Lead4Pass
Candidates use the latest updated CCNP Security 300-725 dumps from Lead4Pass: https://www.leads4pass.com/300-725.html, to help you get past the hurdle and successfully pass the 300-725 SWSA exam.
Lead4Pass 300-725 dumps provide PDF files and a VCE exam engine to help you practice 300-725 SWSA exam questions quickly and easily. The latest updated 300-725 dumps contain 60 exam questions and answers, verified by IT experts to be true and effective.
Share 13 CCNP Security 300-725 dumps PDF:https://drive.google.com/file/d/1AGxV1yasc5xeNeGayahQYmy0EtICiLRy/
Read CCNP Security 300-725 dumps exam questions and answers online:
| Number of exam questions | Release time | Exam name | From | Previous issue |
| 15 | Sep 20, 2022 | Securing the Web with Cisco Web Security Appliance (SWSA) | Lead4Pass | 2021.9.14 |
New Question 1:
What causes authentication failures on a Cisco WSA when LDAP is used for authentication?
A. when the passphrase contains only 5 characters
B. when the passphrase contains characters that are not 7-bit ASCI
C. when the passphrase contains one of the following characters `@ # $ % ^\’
D. when the passphrase contains 50 characters
Correct Answer: B
New Question 2:
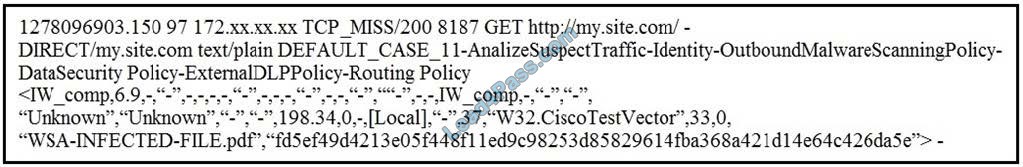
Refer to the exhibit. Which statement about the transaction log is true?
A. The log does not have a date and time
B. The proxy had the content and did not contact other servers
C. The transaction used TCP destination port 8187
D. The AnalizeSuspectTraffic policy group was applied to the transaction
Correct Answer: D
New Question 3:
Which two features can be used with an upstream and downstream Cisco WSA web proxy to have the upstream WSA identify users by their client IP address? (Choose two.)
A. X-Forwarded-For
B. high availability
C. web cache
D. via
E. IP spoofing
Correct Answer: AD
New Question 4:
Which two configuration options are available on a Cisco WSA within a decryption policy? (Choose two.)
A. Pass Through
B. Warn
C. Decrypt
D. Allow
E. Block
Correct Answer: AC
New Question 5:
Which information in the HTTP request is used to determine if it is subject to the referrer exceptions feature in the Cisco WSA?
A. protocol
B. version
C. header
D. payload
Correct Answer: C
Requests for embedded content usually include the address of the site from which the request originated (this is known as the “referer” field in the request\’s HTTP header). This header information is used to determine the categorization of the referred content.
New Question 6:
What is used to configure WSA as an explicit proxy?
A. IP Spoofing from the router
B. Network settings from user browser
C. WCCP redirection from the firewall
D. Auto redirection using PBR from the switch
Correct Answer: B
Reference: https://www.cisco.com/c/en/us/support/docs/security/web-security-appliance/117940-qa-wsa-00.html
New Question 7:
What is the benefit of integrating Cisco Cognitive Threat Analytics with a Cisco WSA?
A. It adds additional information to the Cisco WSA reports
B. It adds additional malware protection to the Cisco WSA
C. It provides the ability to use artificial intelligence to block viruses
D. It reduces time to identify threats in the network
Correct Answer: B
Reference: https://www.ironportstore.com/datasheets/data_sheet_c78-729630.pdf
New Question 8:
What are all of the available options for configuring an exception to blocking for referred content?
A. all embedded/referred and all embedded/referred except
B. selected embedded/referred except, all embedded/referred, and selected embedded/referred
C. selected embedded/referred and all embedded/referred except
D. all embedded/referred, selected embedded/referred, and all embedded/referred except
Correct Answer: D
Reference: https://www.cisco.com/c/en/us/td/docs/security/wsa/wsa11-7/user_guide/b_WSA_UserGuide_11_7/b_WSA_UserGuide_11_7_chapter_01001.html (procedure)
New Question 9:
Which two parameters are mandatory to control access to websites with proxy authentication on a Cisco WSA? (Choose two.)
A. External Authentication
B. Identity Enabled Authentication
C. Transparent User Identification
D. Credential Encryption
E. Authentication Realm
Correct Answer: DE
New Question 10:
What is a valid predefined time range when configuring a Web Tracking query?
A. year
B. minute
C. hour
D. month
Correct Answer: B
Web tracking query uses minute as a predefined time range to track web-related queries.
New Question 11:
When a Cisco WSA is installed with default settings, which port is assigned to the web proxy if the M1 port is used exclusively for management?
A. T1
B. P2
C. T2
D. P1
Correct Answer: D
New Question 12:
Which statement about Cisco Advanced Web Security Reporting integration is true?
A. AWSR uses IP addresses to differentiate Cisco WSA deployments
B. AWSR does not require a license to index data
C. AWSR can remove log files after they are indexed
D. AWSR installation is CLI-based on Windows and Red Hat Linux systems
Correct Answer: D
New Question 13:
A user browses a company website that is categorized as “Business and Industry” and contains a Facebook post. The user cannot see the Facebook post because the category “Social Networking” is blocked. Which configuration allows the user to see the Facebook post?
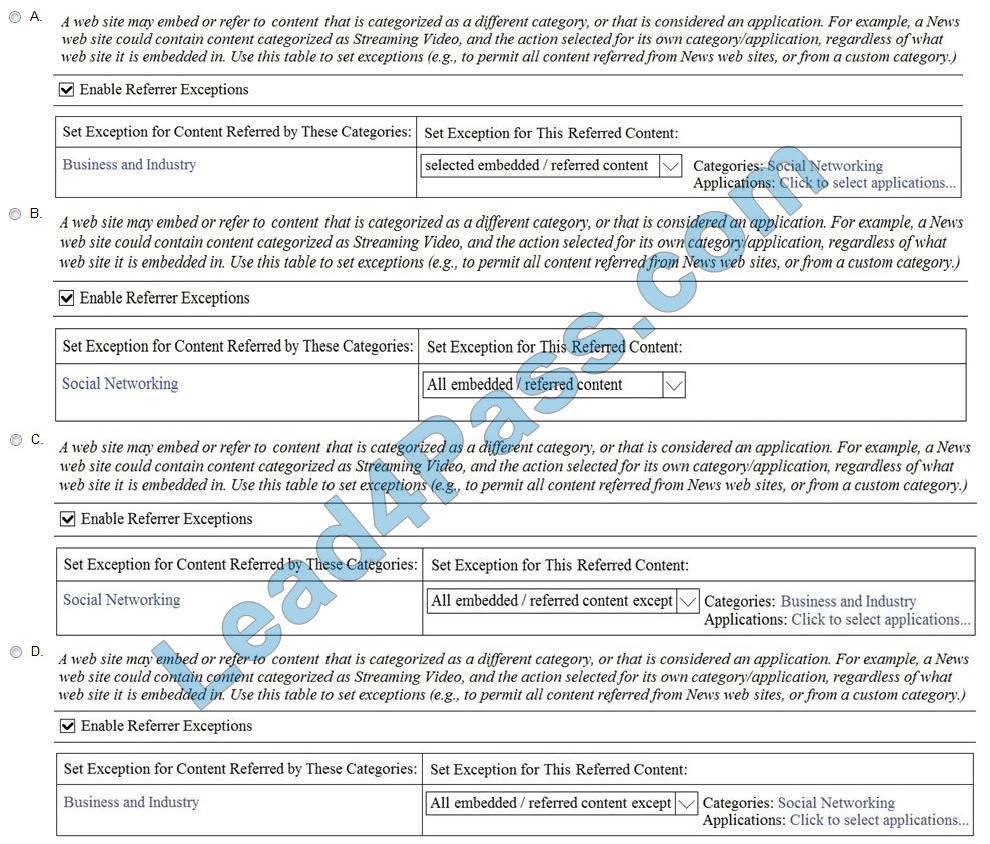
A. Option A
B. Option B
C. Option C
D. Option D
Correct Answer: A
New Question 14:
Which two types of reports are scheduled on the Cisco WSA to analyze traffic? (Choose two.)
A. Layer 3 traffic monitor
B. URL categories
C. host statistics
D. application visibility
E. system capacity
Correct Answer: AD
Reference: https://www.cisco.com/c/en/us/td/docs/security/wsa/wsa11-0/user_guide/b_WSA_UserGuide/b_WSA_UserGuide_chapter_010101.pdf (8)
New Question 15:
What must be configured first when creating an access policy that matches the Active Directory group?
A. authentication, authorization, and accounting of groups
B. FQDN specification
C. authentication realm
D. authorized groups specification
Correct Answer: C
…
Download 13 CCNP Security 300-725 dumps PDF:https://drive.google.com/file/d/1AGxV1yasc5xeNeGayahQYmy0EtICiLRy/
Candidates studying the CCNP Security 300-725 dumps exam questions above can help them improve their exam experience, but this is only a warm-up.
You are welcome to download the latest updated CCNP Security 300-725 dumps: https://www.leads4pass.com/300-725.html, A truly effective route for candidates to pass the 300-725 SWSA exam.
Latest Updated CCNP Security 300-710 Dumps Helps Candidates Pass 300-710 SNCF Exam
The latest updated CCNP Security 300-710 dumps with PDF files and VCE exam engine, containing 238 exam questions and answers, serve all 300-710 SNCF exam candidates to help them successfully pass the exam.
You are welcome to download the latest updated 300-710 dumps: https://www.leads4pass.com/300-710.html, you will also enjoy 365 days of free updates and a 15% discount with discount code “Cisco”.
Download a free 2022 CCNP Security 300-710 dumps PDF online:
https://drive.google.com/file/d/1sLK7jCo14ta8pkXWtVqYxhJW4G6on4pR/
https://drive.google.com/file/d/1_G338eMZrcF7kcR-pWV1IiAzaXe6Vp52/
Free sharing of 15 CCNP Security 300-710 Dumps exam questions and answers:
New Question 1:
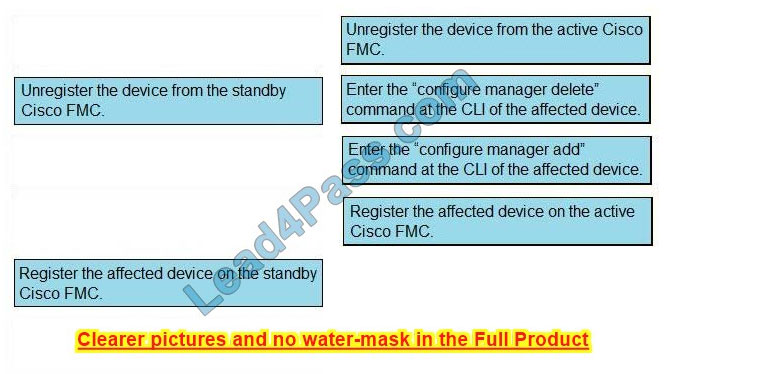
DRAG DROP
Drag and drop the steps to restore an automatic device registration failure on the standby Cisco FMC from the left into the correct order on the right. Not all options are used.
Select and Place:
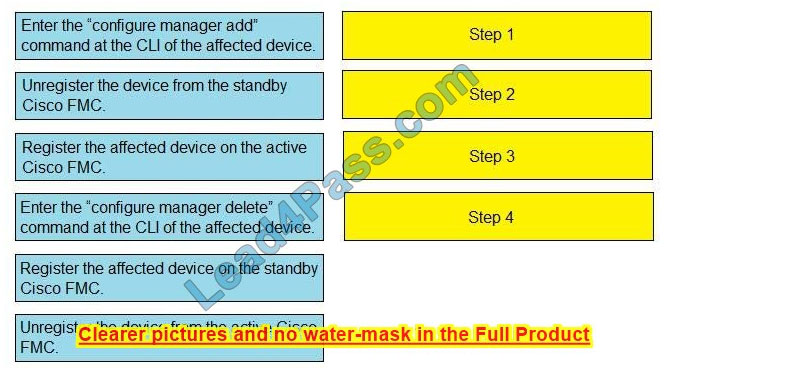
Correct Answer:
New Question 2:
What is the result of enabling Cisco FTD clustering?
A. For the dynamic routing feature, if the master unit fails, the newly elected master unit maintains all existing connections.
B. Integrated Routing and Bridging are supported on the master unit.
C. Site-to-site VPN functionality is limited to the master unit, and all VPN connections are dropped if the master unit fails.
D. All Firepower appliances can support Cisco FTD clustering.
Correct Answer: C
New Question 3:
Which two conditions are necessary for high availability to function between two Cisco FTD devices? (Choose two.)
A. The units must be the same version
B. Both devices can be part of a different group that must be in the same domain when configured within the FMC.
C. The units must be different models if they are part of the same series.
D. The units must be configured only for firewall routed mode.
E. The units must be the same model.
Correct Answer: AE
New Question 4:
On the advanced tab under inline set properties, which allows interfaces to emulate a passive interface?
A. transparent inline mode
B. TAP mode
C. strict TCP enforcement
D. propagate link state
Correct Answer: D
New Question 5:
What are the minimum requirements to deploy a managed device inline?
A. inline interfaces, security zones, MTU, and mode
B. passive interface, MTU, and mode
C. inline interfaces, MTU, and mode
D. passive interface, security zone, MTU, and mode
Correct Answer: C
New Question 6:
What is the difference between an inline and inline tap on Cisco Firepower?
A. Inline tap mode can send a copy of the traffic to another device.
B. Inline tap mode does full packet capture.
C. Inline mode cannot do SSL decryption.
D. Inline mode can drop malicious traffic.
Correct Answer: A
New Question 7:
With Cisco Firepower Threat Defense software, which interface mode must be configured to passively receive traffic that passes through the appliance?
A. inline set
B. passive
C. routed
D. inline tap
Correct Answer: B
New Question 8:
Which two deployment types support high availability? (Choose two.)
A. transparent
B. routed
C. clustered
D. intra-chassis multi-instance
E. virtual appliance in public cloud
Correct Answer: AB
New Question 9:
Which protocol establishes network redundancy in a switched Firepower device deployment?
A. STP
B. HSRP
C. GLBP
D. VRRP
Correct Answer: A
New Question 10:
Which interface type allows packets to be dropped?
A. passive
B. inline
C. ERSPAN
D. TAP
Correct Answer: B
New Question 11:
Which Cisco Firepower Threat Defense, which two interface settings are required when configuring a routed interface? (Choose two.)
A. Redundant Interface
B. EtherChannel
C. Speed
D. Media Type
E. Duplex
Correct Answer: CE
New Question 12:
Which two dynamic routing protocols are supported in Firepower Threat Defense without using FlexConfig? (Choose two.)
A. EIGRP
B. OSPF
C. static routing
D. IS-IS
E. BGP
Correct Answer: BE
New Question 13:
Which policy rule is included in the deployment of a local DMZ during the initial deployment of a Cisco NGFW through the Cisco FMC GUI?
A. a default DMZ policy for which only a user can change the IP addresses.
B. deny IP any
C. no policy rule is included
D. permit IP any
Correct Answer: C
New Question 14:
What are two application layer preprocessors? (Choose two.)
A. CIFS
B. IMAP
C. SSL
D. DNP3
E. ICMP
Correct Answer: BC
New Question 15:
Which two OSPF routing features are configured in Cisco FMC and propagated to Cisco FTD? (Choose two.)
A. OSPFv2 with IPv6 capabilities
B. virtual links
C. SHA authentication to OSPF packets
D. area boundary router type 1 LSA filtering
E. MD5 authentication to OSPF packets
Correct Answer: BE
Download a free 2022 CCNP Security 300-710 dumps PDF online:
https://drive.google.com/file/d/1sLK7jCo14ta8pkXWtVqYxhJW4G6on4pR/
https://drive.google.com/file/d/1_G338eMZrcF7kcR-pWV1IiAzaXe6Vp52/
Here candidates can enjoy free CCNP Security 300-710 exam questions and answers and free PDF downloads, which are historical exam questions to help you grow your experience. Welcome to the new 300-710 SNCF exam, download Lead4Pass 300-710 dumps: https://www.leads4pass.com/300-710.html, to help you successfully pass the exam and achieve a career leap.
More IT certification blogs: [Amazon]awsexamdumps.com, [Oracle]oraclefreedumps.com, [Cisco]Ciscofreedumps.com, [Microsoft]examdumpsbase.com, [Citrix]citrixexamdumps.com
[CompTIA]comptiafreedumps.com, [VMware]vmwarefreedumps.com, [IBM]ibmexamdumps.com, [HP]hpexamdumps.com, [NetApp]NetAppexamdumps.com, [Juniper]juniperexamdumps.com
[Fortinet] fortinetexamdumps.com
VMware 5v0-11.21 dumps: serves all 5v0-11.21 VMware Cloud on AWS Master Specialist exam candidates
The newly updated VMware 5v0-11.21 dumps contains 65 exam questions and answers that candidates can study using the 5v0-11.21 dumps PDF and 5v0-11.21 dumps VCE to help you successfully pass the 5v0-11.21 VMware Cloud on AWS Master Specialist exam.
You are welcome to download the latest VMware 5v0-11.21 dumps: https://www.leads4pass.com/5v0-11-21.html, Lead4Pass 5v0-11.21 dumps serve all candidates taking the 5v0-11.21 VMware Cloud on AWS Master Specialist exam and guarantee you 100% Successfully passed the 5v0-11.21 VMware Cloud on AWS Master Specialist exam.
Download the VMware 5v0-11.21 PDF for free sharing online:
https://drive.google.com/file/d/1fC84delEl_NyGHjm97mg5f3Z-5246sRf/
Share the latest VMware 5v0-11.21 dumps exam questions and answers for free
NEW QUESTION 1:
Which two network types can be extended with VMware HCX Network Extension? (Choose two.)
A. vSphere Distributed Switch VLAN Networks
B. NSX Overlay Networks
C. Trunk Networks
D. vSphere Standard Switch VLAN Networks
E. Private VLAN Networks
Correct Answer: AB
NEW QUESTION 2:
Where would a VMware Cloud on AWS administrator generate an API token?
A. Organizational Settings
B. Identity and Access Management
C. Developer Center
D. My Account Section
Correct Answer: D
NEW QUESTION 3:
A customer wants to ensure that VMware Cloud on AWS maintenance operations are performed during their maintenance window. Which option would allow the customer to achieve this outcome?
A. Schedule a maintenance preference in the software-defined data center (SDDC) console.
B. Schedule a call with VMware Cloud on AWS Support and schedule a maintenance window.
C. Schedule a call with AWS Support and schedule a maintenance window.
D. Schedule a maintenance window through an online support request.
Correct Answer: A
NEW QUESTION 4:
Which method can be used to deploy a VMware Cloud on AWS software-defined data center?
A. VMware Data Center Command-Line Interface
B. AWS Management Console
C. REST APIs
D. VMware vCenter Server
Correct Answer: D
NEW QUESTION 5:
A virtual machine in VMware Cloud on AWS sends a packet to an Amazon Elastic Compute Cloud (EC2) Linux instance in the associated AWS account. Which device is the next hop for the packet?
A. Edge Virtual Machine
B. AWS Elastic Network Adapter (ENA) on the VMware ESXI host
C. Tier-0 (T0) Router
D. Tier-1 (T1) Router
Correct Answer: B
NEW QUESTION 6:
Which two statements are true for the pre-defined resource pools in VMware Cloud on AWS? (Choose two.)
A. Users are allowed to monitor and modify the resource allocation settings in the Mgmt-RsourcePool.
B. The Mgmt-ResourcePool is able to utilize resources in subsequently created clusters if needed.
C. Users can modify the pre-configured vSphere DRS settings in their own Compute-ResourcePool.
D. Users can rename child resource pools to better match company policy.
E. All workload virtual machines are created in the top-level (root) Compute-ResourcePool by default.
Correct Answer: DE
NEW QUESTION 7:
What is the maximum Gbps of bandwidth that each AWS Elastic Network Adapter (ENA) provides on an i3.metal host?
A. 25 Gbps
B. 50 Gbps
C. 10 Gbps
D. 100 Gbps
Correct Answer: A
NEW QUESTION 8:
The Tier-O (TO) router will send northbound packets through which device?
A. The AWS Elastic Network Adapter (ENA) of the VMware ESXi host that the active TO Edge virtual machine is currently running on.
B. The AWS Elastic Network Adapter (ENA) of the VMware ESXi host where the packet is originating from.
C. The AWS Elastic Network Adapter (ENA) of the VMware ESXI host that the passive TO Edge virtual machine is currently running on.
D. The AWS Elastic Network Adapter (ENA) of the VMware ESXi host that is currently the least utilized.
Correct Answer: C
NEW QUESTION 9:
An administrator runs an analysis on all workloads using Live Optics and confirms there are a variety of applications, including Microsoft SQL server and Oracle databases. The Microsoft SQL workloads are averaging 4,000 IOPS per virtual machine, approximately 50% writes. The Oracle workloads are averaging 3,000 IOPS per virtual machine, and approximately 80% writes. Which method should be used to input the data into the VMware Cloud on AWS Sizer for the most accurate results?
A. Use the Advanced Sizer in \’database\’ mode. Create workload profiles for the analyzed virtual machines, including profiles for Microsoft SQL and Oracle. Set the values for vCPU, vRAM, utilized storage, IOPS and I/O profile manually.
B. Use the Quick Sizer. Set the values for vCPU, vRAM, utilized storage, IOPS and I/O profile manually.
C. Use the Advanced Sizer in \’import\’ mode. Import the Live Optics data and let the Advanced Sizer set the values for vCPU, vRAM, utilized storage, IOPS and I/O automatically.
D. Use the Advanced Sizer in \’manual\’ mode. Create workload profiles for the analyzed virtual machines, including profiles for Microsoft SQL and Oracle. Use the default values for the SQL and Oracle workload profiles.
Correct Answer: D
NEW QUESTION 10:
Which three statements are true about the Elastic DRS Optimize for Rapid Scale-Out policy? (Choose three.)
A. Hosts are added incrementally when needed for storage.
B. Hosts will NOT be removed automatically when they are no longer needed.
C. Multiple hosts are added at a time when needed for memory or CPU.
D. After a storage scale-out event is triggered, single hosts are added every 30 minutes.
E. High threshold for storage, like the other policies, is set at 75%.
F. To resolve constraints related to CPU and memory, hosts are added two at a time.
Correct Answer: ACF
NEW QUESTION 11:
A new VMware Cloud on AWS customer has previously deployed a VMware Horizon-based VDI solution into their data center to support their remote developer workforce. Due to unforeseen growth, the company needs to quickly expand their remote workforce. The growth will consume any forecast capacity in the VDI solution and, therefore, additional capacity is now required. The VDI solution service owner would like the solution to support the ability to quickly scale in/out to provide additional capacity based on demand. Which three steps should the administrator take to scale out the VDI solution? (Choose three.)
A. Deploy a new VMware Horizon pod on VMware Cloud on AWS.
B. Deploy a new VMware Horizon pod on-premises.
C. Configure network connectivity and firewall rules to allow communications between the two on-premises connection servers.
D. Configure network connectivity and firewall rules to allow communications between on-premises and VMware Cloud on AWS connection servers.
E. Connect the two VMware Horizon pods together using the security servers.
F. Connect the two VMware Horizon pods together using a Horizon Cloud Pod Architecture (CPA).
Correct Answer: BDF
NEW QUESTION 12:
A user with an Organization Member role would like to add another user to an organization. How would this be accomplished?
A. Only users with an Organization Owner role can invite and add users to the organization.
B. The user with an Organization Member role needs to have CloudAdmin permissions in order to add a new user.
C. The user with an Organization Member role will be able to add a new user through the Identity and Access Management page.
D. Users with an Organization Member role are automatically granted access to all roles within VMware Cloud on AWS.
Correct Answer: A
NEW QUESTION 13:
An administrator is looking to establish a hybrid connection between on-premises and VMware Cloud on AWS software-defined data center (SDDC) environments in order to migrate virtual machines. The on-premises environment is NOT using NSX today; however, the administrator wants to avoid having to change IP addresses after each migration, and there are some applications that require the same broadcast domain. Which connection is needed to meet these requirements?
A. Policy-based VPN
B. Layer 2 VPN (L2VPN)
C. AWS Direct Connect
D. Route-based VPN
Correct Answer: D
…
Download the VMware 5v0-11.21 PDF for free sharing online:
https://drive.google.com/file/d/1fC84delEl_NyGHjm97mg5f3Z-5246sRf/
The above is only a part of VMware 5v0-11.21 dumps exam questions and answers, you can use the above exam questions and answers to improve yourself, not only that, we welcome you to download the latest VMware 5v0-11.21 dumps exam questions: https://www.leads4pass.com/5v0-11-21.html (Total Questions: 65 Q&A), help you truly pass the 5v0-11.21 VMware Cloud on AWS Master Specialist exam.
More IT certification blogs: [Amazon]awsexamdumps.com, [Oracle]oraclefreedumps.com, [Cisco]ciscofreedumps.com, [Microsoft]examdumpsbase.com, [Citrix]citrixexamdumps.com
[CompTIA]CompTIAfreedumps.com, [VMware]vmwarefreedumps.com, [IBM]ibmexamdumps.com, [HP]hpexamdumps.com, [NetApp]NetAppexamdumps.com, [Juniper]juniperexamdumps.com
[Fortinet]fortinetexamdumps.com